Şengül, Gökhan
Loading...
Profile URL
Name Variants
Gokhan, Sengul
Sengul, Gokhan
Sengul,G.
Gökhan, Şengül
Engul G.
Şengül G.
Şengül, Gökhan
G.,Sengul
Sengul, G.
S.,Gokhan
Sengul G.
Ş., Gökhan
G.,Şengül
G., Sengul
Şengül,G.
G., Şengül
S., Gokhan
Ş.,Gökhan
Sengul, Gokhan
Sengul,G.
Gökhan, Şengül
Engul G.
Şengül G.
Şengül, Gökhan
G.,Sengul
Sengul, G.
S.,Gokhan
Sengul G.
Ş., Gökhan
G.,Şengül
G., Sengul
Şengül,G.
G., Şengül
S., Gokhan
Ş.,Gökhan
Job Title
Profesor Doktor
Email Address
gokhan.sengul@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals

Documents
40
Citations
343
h-index
12

Documents
17
Citations
106

Scholarly Output
83
Articles
49
Views / Downloads
104/187
Supervised MSc Theses
9
Supervised PhD Theses
3
WoS Citation Count
217
Scopus Citation Count
331
Patents
0
Projects
0
WoS Citations per Publication
2.61
Scopus Citations per Publication
3.99
Open Access Source
18
Supervised Theses
12
| Journal | Count |
|---|---|
| Biomedical Research (India) | 5 |
| UBMK 2018 - 3rd International Conference on Computer Science and Engineering -- 3rd International Conference on Computer Science and Engineering, UBMK 2018 -- 20 September 2018 through 23 September 2018 -- Sarajevo -- 143560 | 4 |
| 3rd International Conference on Computer Science and Engineering (UBMK) -- SEP 20-23, 2018 -- Sarajevo, BOSNIA & HERCEG | 2 |
| 2016 24th Signal Processing and Communication Application Conference, SIU 2016 - Proceedings -- 24th Signal Processing and Communication Application Conference, SIU 2016 -- 16 May 2016 through 19 May 2016 -- Zonguldak -- 122605 | 2 |
| International Journal of Engineering Education | 2 |
Current Page: 1 / 9
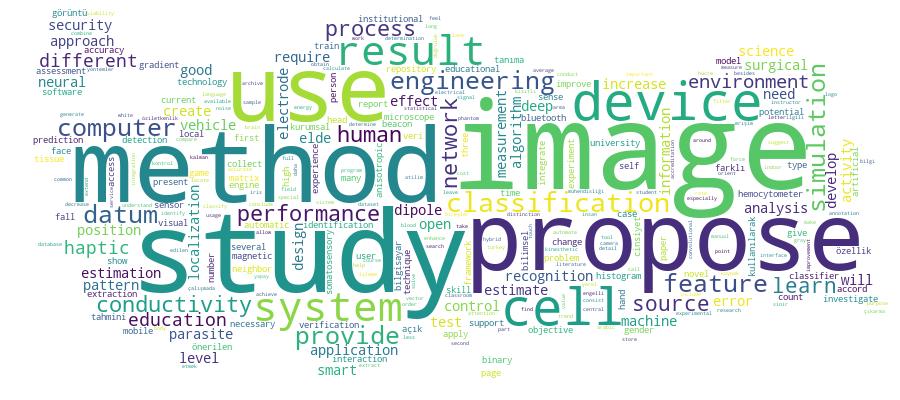
Competency Cloud