Şengül, Gökhan
Loading...
Profile URL
Name Variants
Gokhan, Sengul
Sengul, Gokhan
Sengul,G.
Gökhan, Şengül
Engul G.
Şengül G.
Şengül, Gökhan
G.,Sengul
Sengul, G.
S.,Gokhan
Sengul G.
Ş., Gökhan
G.,Şengül
G., Sengul
Şengül,G.
G., Şengül
S., Gokhan
Ş.,Gökhan
Sengul, Gokhan
Sengul,G.
Gökhan, Şengül
Engul G.
Şengül G.
Şengül, Gökhan
G.,Sengul
Sengul, G.
S.,Gokhan
Sengul G.
Ş., Gökhan
G.,Şengül
G., Sengul
Şengül,G.
G., Şengül
S., Gokhan
Ş.,Gökhan
Job Title
Profesor Doktor
Email Address
gokhan.sengul@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
0
Research Products
 2
2ZERO HUNGER
0
Research Products
 3
3GOOD HEALTH AND WELL-BEING
4
Research Products
 4
4QUALITY EDUCATION
1
Research Products
 5
5GENDER EQUALITY
1
Research Products
 6
6CLEAN WATER AND SANITATION
0
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
1
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
0
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
2
Research Products
 10
10REDUCED INEQUALITIES
0
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
0
Research Products
 13
13CLIMATE ACTION
0
Research Products
 14
14LIFE BELOW WATER
1
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
1
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
0
Research Products

Documents
40
Citations
343
h-index
12

Documents
17
Citations
105

Scholarly Output
83
Articles
49
Views / Downloads
104/171
Supervised MSc Theses
9
Supervised PhD Theses
3
WoS Citation Count
216
Scopus Citation Count
331
Patents
0
Projects
0
WoS Citations per Publication
2.60
Scopus Citations per Publication
3.99
Open Access Source
18
Supervised Theses
12
| Journal | Count |
|---|---|
| Biomedical Research (India) | 5 |
| UBMK 2018 - 3rd International Conference on Computer Science and Engineering -- 3rd International Conference on Computer Science and Engineering, UBMK 2018 -- 20 September 2018 through 23 September 2018 -- Sarajevo -- 143560 | 4 |
| 3rd International Conference on Computer Science and Engineering (UBMK) -- SEP 20-23, 2018 -- Sarajevo, BOSNIA & HERCEG | 2 |
| 2016 24th Signal Processing and Communication Application Conference, SIU 2016 - Proceedings -- 24th Signal Processing and Communication Application Conference, SIU 2016 -- 16 May 2016 through 19 May 2016 -- Zonguldak -- 122605 | 2 |
| International Journal of Engineering Education | 2 |
Current Page: 1 / 9
Scopus Quartile Distribution
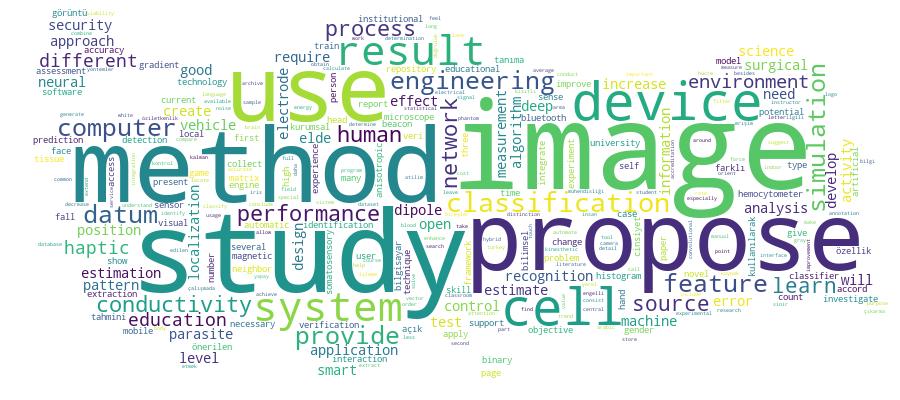
Competency Cloud
83 results
Scholarly Output Search Results
Now showing 1 - 10 of 83
Master Thesis Arapça El Yazısı Harflerin Örüntü Tanıma Yaklaşımları Kullanılarak Tanınması(2017) Douma, Aısha; Şengül, GökhanEl yazısı ile yazılmış harflerin otomatik olarak tanınması; ofis otomasyonu, bankacılık ve güvenlik gibi birçok alanda insanlar ve makineler arasındaki etkileşimi geliştirmek için kullanılır ve insanlar tarafından yazılmış dokümanların makine ile kodlanmış hale dönüştürme sürecidir. Bu tezde, Arapca el yazısı karekterlerin tanınması için gri seviyeli eş oluşum matrisleri (GLCM), yerel ikili örüntü (LBP), yapay sinir ağı (ANN) ve odaklı gradient histogram (HOG) olarak adlandırılan ozellik çıkarma ve sınıflandırma yaklaşımları karşılaştırılmıştır. GLCM, LBP ve HOG özellik çıkarımı için kullanılan yöntemler olup çıkarılan özelliklerden sınıflandırma yapmak için K-en yakın komşu (KNN) sınıflandırma yaklaşımı kullanılmıştır. ANN'de ise sinir ağı girdisi için piksel değerlerinin yoğunlukları kullanılmıştır. Her yöntemin sonuçlarını değerlendirmek için karışıklık matrisi (CM) tekniği ve çapraz geçerleme yöntemleri izlenmiştir. Sonuçlar; HOG (odaklı gradient histogram)'un en yüksek doğruluğu verdiği, en az doğruluk performansının ise gri seviyeli eş oluşum matrisleri tarafından elde edildiği gözlemlenmiştir.Master Thesis Görüntü İşleme Teknikleri Kullanılarak İris Tanıma(2017) Alhamrounı, Mohamed Ahmed; Şengül, Gökhanİris tanıma sistemi yüksek güvenilirlik özelliğinden dolayı özellikle güvenlik alanında çok önemli bir yer edinmiştir. Bir çok araştırmacı sistemin verimliliğini artırmak için iris tanıma sistemine dair öneriler sunmaktadır. Bu tezde ise, iris tanıma sisteminde yüksek performansa ulaşmak için yöntemler önerilmektedir. Bu önerilen sistemde, üç öznitelik çıkarımı yaklaşımı Histogram of Oriented Gradient (HOG) (Yönlü Gradyan Histogramı), Gray Level Co-Occurence Matrix (GLCM) (Gri Düzey Eşdizimlilik Matrisi) ve Local Binary Pattern (LBP) (Yerel İkili Model) iris görüntüsünden özellik çıkarmak için kullanılmıştır. Öte yandan, K-Nearest Neigbors (KNN) (K-En Yakın Komşular) ve Support Vector Machine (SVM) (Destek Vektör Makinesi) ise sınıflandırma aşamasında kullanılmıştır. Iris görüntüsü özellikleri çıkarma aşamasından önce bir kaç aşamadan geçer. Bunların birincisi, tüm görüntülerin yeniden boyutlandırmasını içeren ön-işleme aşaması; ikincisi ise göz görüntüsünde iris bölgesini belirleyen bölütleme aşamasıdır. Son aşama ise, iris bölgesini spesifik boyutlu uygun şekle çeviren normalizasyon evresidir. Önerilen yöntemler, iki iris veritabanında (UPOL ve IITD) test edilmiştir. Bununla birlikte, önerilen sistem HOG+KNN metodu kullandığı zaman % 100'e varan tanıma oranına ulaşmıştır. Anahtar kelimeler: İris tanıma, Yönlü Gradyan Histogramı, Gri Düzey Eşdizimlilik Matrisi, Yerel İkili Model.Article Citation - WoS: 11Citation - Scopus: 12A Comprehensive Assessment Plan for Accreditation in Engineering Education: A Case Study in Turkey(International Journal of Engineering Education, 2015) Turhan, Çiğdem; Şengül, Gökhan; Koyuncu, MuratThis paper describes the procedure followed by Computer Engineering and Software Engineering programs at Atilim University, Ankara, Turkey, which led to the granting of five years of accreditation by MUDEK, the local accreditation body authorized by The European Network for Accreditation of Engineering Education (ENAEE) to award the EUR ACE label, and a full member signatory ofWashington Accord of International Engineering Alliance (IEA). It explains the organizational structure established for preparation, determination and measurement of the educational objectives, program outcomes, course outcomes, and the continuous improvement cycle carried out during the preparation period. The aim of the paper is to share methods and experiences which may be beneficial for the other programs that are intended for accreditation.Article Citation - WoS: 6Citation - Scopus: 12Classification of Parasite Egg Cells Using Gray Level Cooccurence Matrix and Knn(Scientific Publishers india, 2016) Sengul, GokhanParasite eggs are around 20 to 80 mu m dimensions, and they can be seen under microscopes only and their detection requires visual analyses of microscopic images, which requires human expertise and long analysis time. Besides visual analysis is very error prone to human procedures. In order to automatize this process, a number of studies are proposed in the literature. But there is still a gap between the preferred performance and the reported ones and it is necessary to increase the performance of the automatic parasite egg classification approaches. In this study a learning based statistical pattern recognition approach for parasite egg classification is proposed that will both decrease the time required for the manual classification by an expert and increase the performance of the previously suggested automated parasite egg classification approaches. The proposed method uses Gray-Level Co-occurrence Matrix as the feature extractor, which is a texture based statistical method that can differentiate the parasite egg cells based on their textures, and the k-Nearest Neighbourhood (kNN) classifier for the classification. The proposed method is tested on 14 parasite egg types commonly seen in humans. The results show that proposed method can classify the parasite egg cells with a performance rate of 99%.Article Determination of Measurement Noise, Conductivity Errors and Electrode Mislocalization Effects To Somatosensory Dipole Localization(Biomedical Research, 2012) Şengül, Gökhan; Baysal, UğurCalculating the spatial locations, directions and magnitudes of electrically active sources of human brain by using the measured scalp potentials is known as source localization. An accu rate source localization method requires not only EEG data but also the 3-D positions and number of measurement electrodes, the numerical head model of the patient/subject and the conductivities of the layers used in the head model. In this study we computationally deter mined the effect of noise, conductivity errors and electrode mislocalizations for electrical sources located in somatosensory cortex. We first randomly selected 1000 electric sources in somatosensory cortex, and for these sources we simulated the surface potentials by using av erage conductivities given in the literature and 3-D positions of the electrodes. We then added random noise to measurements and by using noisy data; we tried to calculate the positions of the dipoles by using different electrode positions or different conductivity values. The esti mated electrical sources and original ones are compared and by this way the effect of meas urement noise, electrode mislocalizations and conductivity errors to somatosensory dipole lo calization is investigated. We conclude that for an accurate somatosensory source localization method, we need noiseless measurements, accurate conductivity values of scalp and skull lay ers and the accurate knowledge of 3-D positions of measurement sensors.Conference Object Citation - WoS: 1An Undergraduate Curriculum for Deep Learning(Ieee, 2018) Tirkes, Guzin; Ekin, Cansu Cigdem; Sengul, Gokhan; Bostan, Atila; Karakaya, MuratDeep Learning (DL) is an interesting and rapidly developing field of research which has been currently utilized as a part of industry and in many disciplines to address a wide range of problems, from image classification, computer vision, video games, bioinformatics, and handwriting recognition to machine translation. The starting point of this study is the recognition of a big gap between the sector need of specialists in DL technology and the lack of sufficient education provided by the universities. Higher education institutions are the best environment to provide this expertise to the students. However, currently most universities do not provide specifically designed DL courses to their students. Thus, the main objective of this study is to design a novel curriculum including two courses to facilitate teaching and learning of DL topic. The proposed curriculum will enable students to solve real-world problems by applying DL approaches and gain necessary background to adapt their knowledge to more advanced, industry-specific fields.Article Single Camera Photogrammetry System for Eeg Electrode Identification and Localization(Annals of Biomedical Engineering, 2010) Baysal, Uğur; Şengül, GökhanIn this study, photogrammetric coordinate measurement and color-based identification of EEG electrode positions on the human head are simultaneously implemented. A rotating, 2MP digital camera about 20 cm above the subject’s head is used and the images are acquired at predefined stop points separated azimuthally at equal angular displacements. In order to realize full automation, the electrodes have been labeled by colored circular markers and an electrode recognition algorithm has been developed. The proposed method has been tested by using a plastic head phantom carrying 25 electrode markers. Electrode locations have been determined while incorporating three different methods: (i) the proposed photogrammetric method, (ii) conventional 3D radiofrequency (RF) digitizer, and (iii) coordinate measurement machine having about 6.5 lm accuracy. It is found that the proposed system automatically identifies electrodes and localizes them with a maximum error of 0.77 mm. It is suggested that this method may be used in EEG source localization applications in the human brain.Article Classification of Parasite Egg Cells Using Gray Level Cooccurence Matrix and Knn.(Biomedical Research, 2016) Şengül, GökhanParasite eggs are around 20 to 80 μm dimensions, and they can be seen under microscopes only and their detection requires visual analyses of microscopic images, which requires human expertise and long analysis time. Besides visual analysis is very error prone to human procedures. In order to automatize this process, a number of studies are proposed in the literature. But there is still a gap between the preferred performance and the reported ones and it is necessary to increase the performance of the automatic parasite egg classification approaches. In this study a learning based statistical pattern recognition approach for parasite egg classification is proposed that will both decrease the time required for the manual classification by an expert and increase the performance of the previously suggested automated parasite egg classification approaches. The proposed method uses Gray-Level Co-occurrence Matrix as the feature extractor, which is a texture based statistical method that can differentiate the parasite egg cells based on their textures, and the k-Nearest Neighbourhood (kNN) classifier for the classification. The proposed method is tested on 14 parasite egg types commonly seen in humans. The results show that proposed method can classify the parasite egg cells with a performance rate of 99%.Article Bilimsel İletişimde Yeşil ve Altın Yollarda Yakınsama ve Türkiye’deki Yansımaları(Bilgi Dünyası, 2011) Ertürk, Korhan Levent; Şengül, GökhanSon yıllarda özellikle sosyal ağlarda bilgi dolaşımının artması, gelişmiş mobil iletişim cihazlarının yoğun kullanımı kısıtsız ve farklı ortamlarda bilgi erişim ve paylaşımını gerektirmektedir. Bu bağlamda bilimsel bulguların yer aldığı makalelerin geniş kitlelere ve diğer bilim insanlarının erişimine açılması; hem bilimsel eserin doğruluk ve güvenirliğini artırmaya yardımcı olmakta, hem de bilimsel verinin paylaşılmasını ve dolayısı ile de bilimsel gelişimi olumlu yönde etkilemektedir. Yaklaşık on yıldır bu amaca açık erişim insiyatifi katkı sağlamaktadır. Bu amaçla kendi kendine arşivleme (yeşil yol) ve açık erişim dergisi (altın yol) bilimsel çalışmaların bilim topluluğuna sunulmasında yeni yöntemler olarak takdim edilmiştir Bu çalışmada; uluslararası alanda yeşil ve altın yollar üzerinde ortaya konan kurallar irdelenmiş, yazar ve yayıncılarının oluşan iklime uyumluluğu sorgulanmış ve Türkiye adresli kurumsal arşiv ve dergilerin ortaya çıkan durum karşısında konumları üzerine bir değerlendirme yapılmıştır. Çalışma esnasında Ulrich Süreli Yayın Rehberi, Thomson Reuters (ISI) Bilimsel Web (Web of Science - WoS) ve Elsevier Scopus uluslararası ticari atıf veri tabanları, RoMEO, Juliet, ve ROARMAP telif politikası rehberleri, OpenDOAR, ROAR kurumsal arşiv rehberleri ve DOAJ açık erişim dergisi rehberi ile ULAKBİM ulusal veri tabanları incelenmiştir.Article Biometric Verification on E-Id Secure Access Devices: a Case Study on Turkish National E-Id Card Secure Access Device Specifications(International Journal of Information Security Science, 2017) Bostan, Atila; Şengül, Gökhan; Karakaya, MuratBiometric verification on e-ID cards requires clear procedures and standards be defined, especially when the access devices are anticipated to be produced commercial companies. Turkish national e-ID card project has reached the dissemination step. Now the commercial companies are expected to produce and market e-ID card access devices which will conduct secure electronic identity verification functions. However, published standards specifying e-ID card-access-device requirements are ambiguous on biometric verification procedures. In this study, we intended to attract scientific interest to the problems identified in the current design of biometric verification on Turkish national e-ID cards and proposed several verification alternatives which enables the production of e-ID card access devices in a commercial-competition environment.

