Karakaya, Kasım Murat
Loading...

Profile URL
Name Variants
Karakaya, Murat
Karakaya, Kasım Murat
K., Kasim Murat
K.,Kasım Murat
Karakaya,K.M.
Kasim Murat, Karakaya
K., Karakaya
K.,Kasim Murat
Karakaya, Kasim Murat
Kasım Murat, Karakaya
K.M.Karakaya
K.,Karakaya
Karakaya,M.
Karakaya,M.
Karakaya, Kasım Murat
K., Kasim Murat
K.,Kasım Murat
Karakaya,K.M.
Kasim Murat, Karakaya
K., Karakaya
K.,Kasim Murat
Karakaya, Kasim Murat
Kasım Murat, Karakaya
K.M.Karakaya
K.,Karakaya
Karakaya,M.
Karakaya,M.
Job Title
Profesör Doktor
Email Address
murat.karakaya@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Former Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
0
Research Products
 2
2ZERO HUNGER
0
Research Products
 3
3GOOD HEALTH AND WELL-BEING
1
Research Products
 4
4QUALITY EDUCATION
0
Research Products
 5
5GENDER EQUALITY
0
Research Products
 6
6CLEAN WATER AND SANITATION
0
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
1
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
0
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
0
Research Products
 10
10REDUCED INEQUALITIES
0
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
4
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
0
Research Products
 13
13CLIMATE ACTION
0
Research Products
 14
14LIFE BELOW WATER
0
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
0
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
0
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
44
Articles
20
Views / Downloads
30/40
Supervised MSc Theses
4
Supervised PhD Theses
0
WoS Citation Count
142
Scopus Citation Count
205
Patents
0
Projects
0
WoS Citations per Publication
3.23
Scopus Citations per Publication
4.66
Open Access Source
4
Supervised Theses
4
| Journal | Count |
|---|---|
| UBMK 2018 - 3rd International Conference on Computer Science and Engineering -- 3rd International Conference on Computer Science and Engineering, UBMK 2018 -- 20 September 2018 through 23 September 2018 -- Sarajevo -- 143560 | 4 |
| 2017 IEEE 1st Ukraine Conference on Electrical and Computer Engineering, UKRCON 2017 - Proceedings -- 1st IEEE Ukraine Conference on Electrical and Computer Engineering, UKRCON 2017 -- 29 May 2017 through 2 June 2017 -- Kyiv -- 131763 | 2 |
| Proceedings - 6th International Conference on Computer Science and Engineering, UBMK 2021 -- 6th International Conference on Computer Science and Engineering, UBMK 2021 -- 15 September 2021 through 17 September 2021 -- Ankara -- 176826 | 2 |
| 3rd International Conference on Computer Science and Engineering (UBMK) -- SEP 20-23, 2018 -- Sarajevo, BOSNIA & HERCEG | 2 |
| 1st International Informatics and Software Engineering Conference: Innovative Technologies for Digital Transformation, IISEC 2019 - Proceedings -- 1st International Informatics and Software Engineering Conference, IISEC 2019 -- 6 November 2019 through 7 November 2019 -- Ankara -- 157111 | 2 |
Current Page: 1 / 5
Scopus Quartile Distribution
Competency Cloud
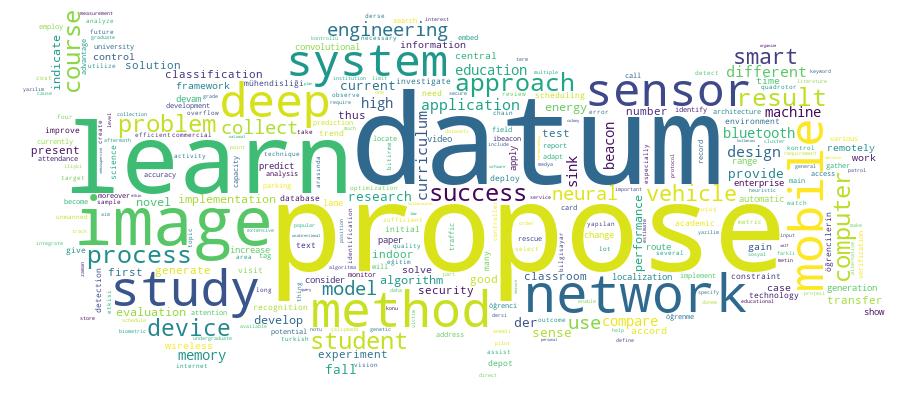
22 results
Scholarly Output Search Results
Now showing 1 - 10 of 22
Article Citation - WoS: 50Citation - Scopus: 70Deep Learning Based Fall Detection Using Smartwatches for Healthcare Applications(Elsevier Sci Ltd, 2022) Sengul, Gokhan; Karakaya, Murat; Misra, Sanjay; Abayomi-Alli, Olusola O.; Damasevicius, RobertasWe implement a smart watch-based system to predict fall detection. We differentiate fall detection from four common daily activities: sitting, squatting, running, and walking. Moreover, we separate falling into falling from a chair and falling from a standing position. We develop a mobile application that collects the acceleration and gyroscope sensor data and transfers them to the cloud. In the cloud, we implement a deep learning algorithm to classify the activity according to the given classes. To increase the number of data samples available for training, we use the Bica cubic Hermite interpolation, which allows us to improve the accuracy of the neural network. The 38 statistical data features were calculated using the rolling update approach and used as input to the classifier. For activity classification, we have adopted the bi-directional long short-term memory (BiLSTM) neural network. The results demonstrate that our system can detect falling with an accuracy of 99.59% (using leave-one-activityout cross-validation) and 97.35% (using leave-one-subject-out cross-validation) considering all activities. When considering only binary classification (falling vs. all other activities), perfect accuracy is achieved.Article Citation - WoS: 5Citation - Scopus: 7Deadline-Aware Energy-Efficient Query Scheduling in Wireless Sensor Networks With Mobile Sink(Hindawi Ltd, 2013) Karakaya, MuratMobile sinks are proposed to save sensor energy spent for multihop communication in transferring data to a base station (sink) in Wireless Sensor Networks. Due to relative low speed of mobile sinks, these approaches are mostly suitable for delay-tolerant applications. In this paper, we study the design of a query scheduling algorithmfor query-based data gathering applications using mobile sinks. However, these kinds of applications are sensitive to delays due to specified query deadlines. Thus, the proposed scheduling algorithm aims to minimize the number of missed deadlines while keeping the level of energy consumption at the minimum.Article Using Bluetooth Low Energy Beacons for Indoor Localization(International Journal of Intelligent Systems and Applications in Engineering, 2017) Şengül, Gökhan; Karakaya, MuratBluetooth Low Energy (BLE) Beacons gain high popularity due to their low consumption of energy and, thereby, long lifetime. Using the BLE protocol, these devices emit advertisement packets at fixed intervals for a short duration. Indoor localization solutions aim to provide an accurate, low cost estimate of sub-room indoor positioning. There are various techniques proposed for this purpose. BLE Beacons are good hardware candidates to assist the creation of such indoor localization solutions. Given the exact position of BLE Beacons, one can attempt to estimate a receiver position according to the received signal power. In this work, we investigated the success of such an indoor localization approach employing multiple BLE Beacons and two different estimation techniques. The results of the experiments indicate that employing multiple BLE Beacons increases the success of prediction techniques considerably.Article A Smart Classroom Application: Monitoring and Reporting Attendance Automatically Using Smart Devices(International Journal of Scientific Research in Information Systems and Engineering, 2017) Şengül, Gökhan; Karakaya, Murat; Bostan, AtilaFor recording attendance in a classroom, generally instructors collect signatures of the attendees. Then, at the end of the semester, those signatures need to be counted and reported. This process causes waste of time and effort for both instructors and attendees. Besides this process is very error prone. Moreover, in crowded classes, there could be some misuses of this process. In this study, a smart classroom application is proposed and developed in order to monitor the attendance of the students in a classroom environment. In the design, a low-energy Bluetooth device is located at each classroom. Identification number (ID) of the low-energy Bluetooth device and the name/number of the classroom that the device is located are matched and stored in a central database. In addition to this information, the name of the courses given in that classroom and their time tables are also stored in the central database. Thus, in the database, the weekly course schedule of the classrooms is available. In addition to this central database infrastructure, a mobile application is developed that can run on both in mobile phones and smart watches. The users first install the application on their own smart devices. Whenever an attendee enters to a classroom, the smart device and its application interacts with the low-energy Bluetooth device. The student’s identification number (Student ID: SID), the identification number (ID) of the low-energy Bluetooth device located at the class, the day and time of the interaction are sent to the central database by the smart device. Using this information, the name of the attendee and the courses that he/she attended are matched using the SID of the attendee, the ID of the low-energy Bluetooth device, the day and time of the interaction. Those matching information are also stored in the central database. The records in the central database are used to create any automatic reports, i.e. the attendance status, the time and duration of the attendance, and the classroom (course) of the record. The advantage of the proposed system is that it is a fully automatic system that records the presence of the students, generates automatic attendance reports, does not require any extra device except installing a mobile application onto smart phones or smart watches of the student, and can be deployed with a low budget. The proposed system is tested in real classroom environment and it is proven to be operational.Article Citation - WoS: 78Citation - Scopus: 93Efficient Route Planning for an Unmanned Air Vehicle Deployed on a Moving Carrier(Springer, 2016) Savuran, Halil; Karakaya, MuratVehicle routing problem (VRP) is a constrained extension of the well-known traveling salesman problem (TSP). Emerging from the current conceptual trends in operations field, a new constraint to be included to the existing VRP parameters is the depot mobility. A practical example of such a problem is planning a route for an Unmanned air vehicle (UAV) deployed on a mobile platform to visit fixed targets. Furthermore, the range constraint of the UAV becomes another constraint within this sample case as well. In this paper, we define new VRP variants by introducing depot mobility (Mobile Depot VRP: MoDVRP) and extending it with capacity constraint (Capacitated MoDVRP: C-MoDVRP). As a sample use case, we study route planning for a UAV deployed on a moving carrier. To deal with the C-MoDVRP, we propose a Genetic Algorithm that is adapted to satisfy the constraints of depot mobility and range, while maximizing the number of targets visited by the UAV. To examine the success of our approach, we compare the individual performances of our proposed genetic operators with conventional ones and the performance of our overall solution with the Nearest Neighbor and Hill Climbing heuristics, on some well-known TSP benchmark problems, and receive successful results.Article Determination and Identification of Dangerously Lane Changing Vehicles in Traffic by Image Processing Techniques(International Journal of Scientific Research in Information Systems and Engineering, 2017) Şengül, Gökhan; Karakaya, Murat; Bostan, AtilaDue to increase of vehicle usage all around the world, the importance of safety driving in traffic is increasing. All of the countries around the world are taking actions to increase the safety driving habitats and decrease the number of traffic accidents. One of the applied precautions is to put necessary automatic auditing mechanisms into service for controlling the drivers as they drive since reckless drivers may not obey many traffic rules. In this study, image and video processing based methods are applied to identify the dangerously lane changing vehicles/drivers in the traffic. The proposed method focuses on to detect three different violations in traffic: the vehicles frequently changing traffic lanes, the vehicles changing lanes when it is forbidden, and the vehicles overtaking the other vehicles using the right lanes instead of left one. The proposed method is based on the image and video processing techniques. It first detects the vehicles in video sequences, then tracks the vehicles in the following frames and determines the lane changes of the vehicles. In the vehicle detection phase an image subtraction method is used. In the vehicle tracking phase, Kalman filtering tracking algorithm is used. After determining the lane changes of the vehicles/drivers, a rule based decision system is used to find out the vehicles/drivers improperly changing lanes and those vehicles are marked on the video. The proposed method is tested on the videos captured from real traffic environments and promising results are obtained.Conference Object Citation - WoS: 1An Undergraduate Curriculum for Deep Learning(Ieee, 2018) Tirkes, Guzin; Ekin, Cansu Cigdem; Sengul, Gokhan; Bostan, Atila; Karakaya, MuratDeep Learning (DL) is an interesting and rapidly developing field of research which has been currently utilized as a part of industry and in many disciplines to address a wide range of problems, from image classification, computer vision, video games, bioinformatics, and handwriting recognition to machine translation. The starting point of this study is the recognition of a big gap between the sector need of specialists in DL technology and the lack of sufficient education provided by the universities. Higher education institutions are the best environment to provide this expertise to the students. However, currently most universities do not provide specifically designed DL courses to their students. Thus, the main objective of this study is to design a novel curriculum including two courses to facilitate teaching and learning of DL topic. The proposed curriculum will enable students to solve real-world problems by applying DL approaches and gain necessary background to adapt their knowledge to more advanced, industry-specific fields.Article Citation - Scopus: 1Analyzing Students' Academic Success in Pre-requisite Course Chains: A Case Study in Turkey(Tempus Publications, 2018) Karakaya, Murat; Eryilmaz, Meltem; Ceyhan, Ulas; Computer EngineeringThere are several principles which have been accepted as approaches to successful curriculum development. In spite of the differences in the proposed sequencing of topics, all approaches basically depend on the pre-requisite chains to implement their educational approach in the curriculum development for specifying the order of the subjects. In this research, two prerequisite chains representing two different curriculum development approaches are taken into consideration in a case study. The first research question considered is whether academic success in a follow-up course is positively related to success attained in the pre-requisite course. The second one is whether or not the selected curriculum development approach for deciding the chains has a significant impact on the academic success relationships between a pre-requisite and its follow-up course. To answer these questions, course data of 441 undergraduate students who graduated from the Atilim University between Fall 2001 and Spring 2015 semesters were collected and analyzed. The results indicate that the succes levels gained in a pre-requisite and its follow-up course are corelated. Moreover, different cirriculum development methods can affect this corelation. Thus, cirriculum developers should consider appropriate approaches to improve student success for deciding chaining courses and their contents.Article Citation - WoS: 1Citation - Scopus: 1Msct: an Efficient Data Collection Heuristic for Wireless Sensor Networks With Limited Sensor Memory Capacity(Ksii-kor Soc internet information, 2015) Karakaya, MuratSensors used in Wireless Sensor Networks (WSN) have mostly limited capacity which affects the performance of their applications. One of the data-gathering methods is to use mobile sinks to visit these sensors so that they can save their limited battery energies from forwarding data packages to static sinks. The main disadvantage of employing mobile sinks is the delay of data collection due to relative low speed of mobile sinks. Since sensors have very limited memory capacities, whenever a mobile sink is too late to visit a sensor, that sensor's memory would be full, which is called a 'memory overflow', and thus, needs to be purged, which causes loss of collected data. In this work, a method is proposed to generate mobile sink tours, such that the number of overflows and the amount of lost data are minimized. Moreover, the proposed method does not need either the sensor locations or sensor memory status in advance. Hence, the overhead stemmed from the information exchange of these requirements are avoided. The proposed method is compared with a previously published heuristic. The simulation experiment results show the success of the proposed method over the rival heuristic with respect to the considered metrics under various parameters.Article Unidirectional Data Transfer: a Secure System To Push the Data From a High Security Network To a Lower One Over an Actual Air-Gap(International Journal of Scientific Research in Information Systems and Engineering, 2017) Şengül, Gökhan; Bostan, Atila; Karakaya, MuratThe term “air-gap” is typically used to refer physical and logical separation of two computer networks. This type of a separation is generally preferred when the security levels of the networks are not identical. Although the security requirements entail parting the data networks, there is a growing need for fast and automatic transfer of data especially from high-security networks to low-security ones. To protect security sensitive system from the risks originating from low-security network, unidirectional connections that permit the data transfer only from high to low-security network, namely information-diodes, are in use. Nonetheless, each diode solution has its drawbacks either in performance or security viewpoints. In this study, we present a unidirectional data transfer system in which the primary focus is data and signal security in technical design and with a plausible and adaptable data transfer performance. Such that the networks do not touch each other either in physically or logically and the transfer is guaranteed to be unidirectional. Apart from avoiding the malicious transmissions from low to high-security network, we claim that the proposed data diode design is safe from emanation leakage with respect to the contemporary sniffing and spoofing techniques.
- «
- 1 (current)
- 2
- 3
- »

