Mısra, Sanjay
Loading...

Profile URL
Name Variants
M.,Sanjay
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Job Title
Profesör Doktor
Email Address
sanjay.misra@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
3
Research Products
 2
2ZERO HUNGER
5
Research Products
 3
3GOOD HEALTH AND WELL-BEING
2
Research Products
 4
4QUALITY EDUCATION
6
Research Products
 5
5GENDER EQUALITY
2
Research Products
 6
6CLEAN WATER AND SANITATION
1
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
8
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
11
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
11
Research Products
 10
10REDUCED INEQUALITIES
2
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
3
Research Products
 13
13CLIMATE ACTION
7
Research Products
 14
14LIFE BELOW WATER
10
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
4
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
9
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
199
Articles
133
Views / Downloads
686/271
Supervised MSc Theses
3
Supervised PhD Theses
0
WoS Citation Count
2629
Scopus Citation Count
3894
Patents
0
Projects
0
WoS Citations per Publication
13.21
Scopus Citations per Publication
19.57
Open Access Source
53
Supervised Theses
3
| Journal | Count |
|---|---|
| Acta Polytechnica Hungarica | 12 |
| Tehnicki Vjesnik | 8 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 2011 International Conference on Computational Science and Its Applications, ICCSA 2011 -- 20 June 2011 through 23 June 2011 -- Santander -- 85480 | 5 |
| Journal of Physics: Conference Series -- 3rd International Conference on Computing and Applied Informatics 2018, ICCAI 2018 -- 18 September 2018 through 19 September 2018 -- Medan, Sumatera Utara -- 149865 | 4 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 12th International Conference on Computational Science and Its Applications, ICCSA 2012 -- 18 June 2012 through 21 June 2012 -- Salvador de Bahia -- 90945 | 4 |
Current Page: 1 / 22
Scopus Quartile Distribution
Competency Cloud
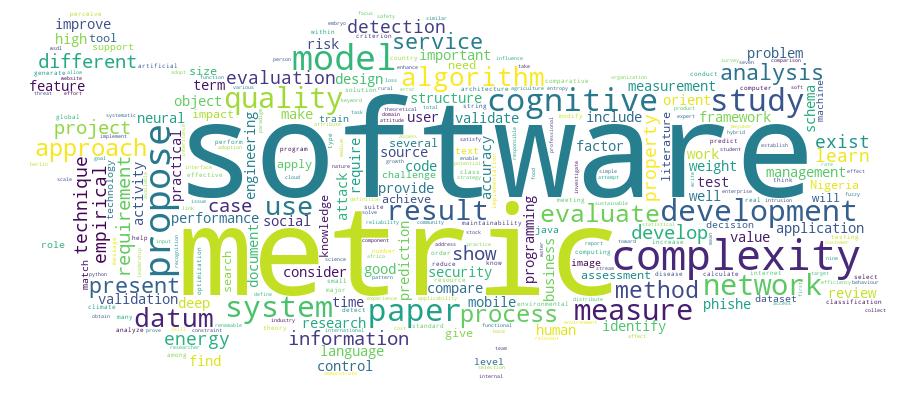
123 results
Scholarly Output Search Results
Now showing 1 - 10 of 123
Article Citation - WoS: 38Citation - Scopus: 59Career Abandonment Intentions among Software Workers(Wiley, 2014) Colomo-Palacios, Ricardo; Casado-Lumbreras, Cristina; Misra, Sanjay; Soto-Acosta, PedroWithin the software development industry, human resources have been recognized as one of the most decisive and scarce resources. Today, the retention of skilled IT (information technology) personnel is a major issue for employers and recruiters as well, since IT career abandonment is a common practice and means not only the loss of personnel, knowledge, and skills, but also the loss of business opportunities. This article seeks to discover the main motivations young practitioners abandon the software career. To achieve this objective, two studies were conducted. The first study was qualitative (performed through semistructured interviews) and intended to discover the main variables affecting software career abandonment. The second study was quantitative, consisting of a Web-based survey developed from the output of the first study and administered to a sample of 148 IT practitioners. Results show that work-related, psychological, and emotional variable are the most relevant group of variables explaining IT career abandonment. More specifically, the three most important variables that motivate employees to abandon the career are effort-reward imbalance, perceived workload, and emotional exhaustion. In contrast, variables such as politics and infighting, uncool work, and insufficient resources influence to a lesser extent the decision to leave the career. (c) 2012 Wiley Periodicals, Inc.Article Citation - WoS: 104Citation - Scopus: 163Cassava Disease Recognition From Low-Quality Images Using Enhanced Data Augmentation Model and Deep Learning(Wiley, 2021) Abayomi-Alli, Olusola Oluwakemi; Damasevicius, Robertas; Misra, Sanjay; Maskeliunas, RytisImprovement of deep learning algorithms in smart agriculture is important to support the early detection of plant diseases, thereby improving crop yields. Data acquisition for machine learning applications is an expensive task due to the requirements of expert knowledge and professional equipment. The usability of any application in a real-world setting is often limited by unskilled users and the limitations of devices used for acquiring images for classification. We aim to improve the accuracy of deep learning models on low-quality test images using data augmentation techniques for neural network training. We generate synthetic images with a modified colour value distribution to expand the trainable image colour space and to train the neural network to recognize important colour-based features, which are less sensitive to the deficiencies of low-quality images such as those affected by blurring or motion. This paper introduces a novel image colour histogram transformation technique for generating synthetic images for data augmentation in image classification tasks. The approach is based on the convolution of the Chebyshev orthogonal functions with the probability distribution functions of image colour histograms. To validate our proposed model, we used four methods (resolution down-sampling, Gaussian blurring, motion blur, and overexposure) for reducing image quality from the Cassava leaf disease dataset. The results based on the modified MobileNetV2 neural network showed a statistically significant improvement of cassava leaf disease recognition accuracy on lower-quality testing images when compared with the baseline network. The model can be easily deployed for recognizing and detecting cassava leaf diseases in lower quality images, which is a major factor in practical data acquisition.Article Citation - Scopus: 48Identifying Phishing Attacks in Communication Networks Using Url Consistency Features(Inderscience Publishers, 2020) Azeez,N.A.; Salaudeen,B.B.; Misra,S.; Damasevicius,R.; Maskeliunas,R.Phishing is a fraudulent attempt by cybercriminals, where the target audience is addressed by a text message, phone call or e-mail, requesting classified and sensitive information after presenting himself/herself as a legitimate agent. Successful phishing attack may result into financial loss and identity theft. Identifying forensic characteristics of phishing attack can help to detect the attack and its perpetuators and as well as to enable defence against it. To shield internet users from phishing assaults, numerous anti-phishing models have been proposed. Currently employed techniques to handle these challenges are not sufficient and capable enough. We aim at identifying phishing sites in order to guard internet users from being vulnerable to any form of phishing attacks by verifying the conceptual and literal consistency between the uniform resource locator (URL) and the web content. The implementation of the proposed PhishDetect method achieves an accuracy of 99.1%; indicating that it is effective in detecting various forms of phishing attacks. © 2020 Inderscience Enterprises Ltd.. All rights reserved.Article Citation - WoS: 31Citation - Scopus: 50Neural Network and Classification Approach in Identifying Customer Behavior in the Banking Sector: a Case Study of an International Bank(Wiley, 2015) Ogwueleka, Francisca Nonyelum; Misra, Sanjay; Colomo-Palacios, Ricardo; Fernandez, LuisThe customer relationship focus for banks is in development of main competencies and strategies of building strong profitable customer relationships through considering and managing the customer impression, influence on the culture of the bank, satisfactory treatment, and assessment of valued relationship building. Artificial neural networks (ANNs) are used after data segmentation and classification, where the designed model register records into two class sets, that is, the training and testing sets. ANN predicts new customer behavior from previously observed customer behavior after executing the process of learning from existing data. This article proposes an ANN model, which is developed using a six-step procedure. The back-propagation algorithm is used to train the ANN by adjusting its weights to minimize the difference between the current ANN output and the desired output. An evaluation process is conducted to determine whether the ANN has learned how to perform. The training process is halted periodically, and its performance is tested until an acceptable result is obtained. The principles underlying detection software are grounded in classical statistical decision theory.Article Citation - WoS: 10Citation - Scopus: 18Evaluation Criteria for Object-Oriented Metrics(Budapest Tech, 2011) Misra, Sanjay; Computer EngineeringIn this paper an evaluation model for object-oriented (OO) metrics is proposed. We have evaluated the existing evaluation criteria for OO metrics, and based on the observations, a model is proposed which tries to cover most of the features for the evaluation of OO metrics. The model is validated by applying it to existing OO metrics. In contrast to the other existing criteria, the proposed model is simple in implementation and includes the practical and important aspects of evaluation; hence it suitable to evaluate and validate any OO complexity metric.Article Citation - WoS: 8Citation - Scopus: 18Featuring Cio: Roles, Skills and Soft Skills(Igi Global, 2013) Cano, Carmen; Fernandez-Sanz, Luis; Misra, SanjayThis paper describes how the CIO (Chief Information Officer) position appears as a key role in the organizations and the requirements for candidates. The authors compare the requirements presented in different studies to know what are the most important skills for a successful performance as a CIO. They stress the importance of non technical skills as key factors for professional performance. The authors have compared soft skills for CIO or equivalent positions and other professional profiles like programmers or analysts using data taken from thousands of job ads. An overview of the most valuable skills (especially soft skills) for CIOS is presented.Article Citation - WoS: 20Citation - Scopus: 28Bug Severity Assessment in Cross Project Context and Identifying Training Candidates(World Scientific Publ Co Pte Ltd, 2017) Singh, V. B.; Misra, Sanjay; Sharma, MeeraThe automatic bug severity prediction will be useful in prioritising the development efforts, allocating resources and bug fixer. It needs historical data on which classifiers can be trained. In the absence of such historical data cross project prediction provides a good solution. In this paper, our objective is to automate the bug severity prediction by using a bug metric summary and to identify best training candidates in cross project context. The text mining technique has been used to extract the summary terms and trained the classifiers using these terms. About 63 training candidates have been designed by combining seven datasets of Eclipse projects to develop the severity prediction models. To deal with the imbalance bug data problem, we employed two approaches of ensemble by using two operators available in RapidMiner: Vote and Bagging. Results show that k-Nearest Neighbour (k-NN) performance is better than the Support Vector Machine (SVM) performance. Naive Bayes f-measure performance is poor, i.e. below 34.25%. In case of k-NN, developing training candidates by combining more than one training datasets helps in improving the performances (f-measure and accuracy). The two ensemble approaches have improved the f-measure performance up to 5% and 10% respectively for the severity levels having less number of bug reports in comparison of major severity level. We have further motivated the paper with a cross project bug severity prediction between Eclipse and Mozilla products. Results show that Mozilla products can be used to build reliable prediction models for Eclipse products and vice versa in case of SVM and k-NN classifiers.Article Citation - WoS: 10A DISCUSSION ON ASSURING SOFTWARE QUALITY IN SMALL AND MEDIUM SOFTWARE ENTERPRISES: AN EMPIRICAL INVESTIGATION(Univ Osijek, Tech Fac, 2011) Pusatli, O. Tolga; Misra, SanjayUnder the studies of general core activities including software inspection, review and testing to achieve quality objectives in small-medium size enterprises (SMEs), the paper presents a contemporary view of such companies against quality measures. The results from a local empirical investigation of quality standards in the Turkish software industry are reported. Around 150 software companies have been approached from which 17 detailed feedback inform that in order to ensure software quality, standards including internationally recognized International Standards Organization (ISO) and Capability Maturity Model Integration (CMMI) are given credit. However the substantial workload and resources required to obtain them are also reported as serious; downscaled frameworks of such large models proposed in the literature are not well known by the SMEs either. The paper also discusses "work around" that bypasses such standards to ease delivery of products while keeping certificates as labels just to acquire new jobs for the business.Article Citation - WoS: 25Identifying Phishing Attacks in Communication Networks Using Url Consistency Features(inderscience Enterprises Ltd, 2020) Azeez, Nureni Ayofe; Salaudeen, Balikis Bolanle; Misra, Sanjay; Damasevicius, Robertas; Maskeliunas, RytisPhishing is a fraudulent attempt by cybercriminals, where the target audience is addressed by a text message, phone call or e-mail, requesting classified and sensitive information after presenting himself/herself as a legitimate agent. Successful phishing attack may result into financial loss and identity theft. Identifying forensic characteristics of phishing attack can help to detect the attack and its perpetuators and as well as to enable defence against it. To shield internet users from phishing assaults, numerous anti-phishing models have been proposed. Currently employed techniques to handle these challenges are not sufficient and capable enough. We aim at identifying phishing sites in order to guard internet users from being vulnerable to any form of phishing attacks by verifying the conceptual and literal consistency between the uniform resource locator (URL) and the web content. The implementation of the proposed PhishDetect method achieves an accuracy of 99.1%; indicating that it is effective in detecting various forms of phishing attacks.Article Citation - WoS: 67Citation - Scopus: 90Towards a Social and Context-Aware Mobile Recommendation System for Tourism(Elsevier, 2017) Colomo-Palacios, Ricardo; Jose Garcia-Penalvo, Francisco; Stantchev, Vladimir; Misra, Sanjay; García-Peñalvo, Francisco JoséLoyalty in tourism is one of the main concerns for tourist organizations and researchers alike. Recently, technology in general and CRM and social networks in particular have been identified as important enablers for loyalty in tourism. This paper presents POST-VIA 360, a platform devoted to support the whole life-cycle of tourism loyalty after the first visit. The system is designed to collect data from the initial visit by means of pervasive approaches. Once data is analysed, POST-VIA 360 produces accurate after visit data and, once returned, is able to offer relevant recommendations based on positioning and bio-inspired recommender systems. To validate the system, a case study comparing recommendations from the POST-VIA 360 and a group of experts was conducted. Results show that the accuracy of system's recommendations is remarkable compared to previous efforts in the field. (C) 2016 Elsevier B.V. All rights reserved.

