Mısra, Sanjay
Loading...

Profile URL
Name Variants
M.,Sanjay
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Job Title
Profesör Doktor
Email Address
sanjay.misra@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
3
Research Products
 2
2ZERO HUNGER
5
Research Products
 3
3GOOD HEALTH AND WELL-BEING
2
Research Products
 4
4QUALITY EDUCATION
6
Research Products
 5
5GENDER EQUALITY
2
Research Products
 6
6CLEAN WATER AND SANITATION
1
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
8
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
11
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
11
Research Products
 10
10REDUCED INEQUALITIES
2
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
3
Research Products
 13
13CLIMATE ACTION
7
Research Products
 14
14LIFE BELOW WATER
10
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
4
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
9
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
199
Articles
133
Views / Downloads
686/271
Supervised MSc Theses
3
Supervised PhD Theses
0
WoS Citation Count
2629
Scopus Citation Count
3894
Patents
0
Projects
0
WoS Citations per Publication
13.21
Scopus Citations per Publication
19.57
Open Access Source
53
Supervised Theses
3
| Journal | Count |
|---|---|
| Acta Polytechnica Hungarica | 12 |
| Tehnicki Vjesnik | 8 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 2011 International Conference on Computational Science and Its Applications, ICCSA 2011 -- 20 June 2011 through 23 June 2011 -- Santander -- 85480 | 5 |
| Journal of Physics: Conference Series -- 3rd International Conference on Computing and Applied Informatics 2018, ICCAI 2018 -- 18 September 2018 through 19 September 2018 -- Medan, Sumatera Utara -- 149865 | 4 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 12th International Conference on Computational Science and Its Applications, ICCSA 2012 -- 18 June 2012 through 21 June 2012 -- Salvador de Bahia -- 90945 | 4 |
Current Page: 1 / 22
Scopus Quartile Distribution
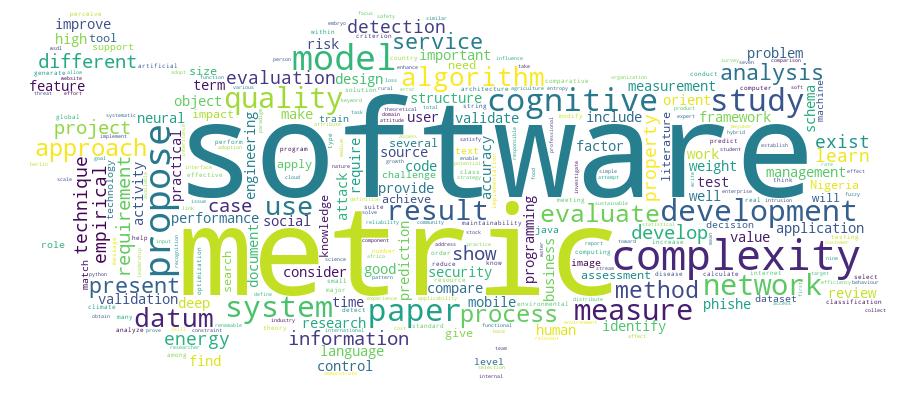
Competency Cloud
21 results
Scholarly Output Search Results
Now showing 1 - 10 of 21
Review Citation - WoS: 3Citation - Scopus: 9An Empirical Evaluation of Software Quality Assurance Practices and Challenges in a Developing Country: a Comparison of Nigeria and Turkey(Springer international Publishing Ag, 2016) Sowunmi, Olaperi Yeside; Mısra, Sanjay; Misra, Sanjay; Fernandez-Sanz, Luis; Crawford, Broderick; Soto, Ricardo; Mısra, Sanjay; Computer Engineering; Computer EngineeringBackground: The importance of quality assurance in the software development process cannot be overemphasized because its adoption results in high reliability and easy maintenance of the software system and other software products. Software quality assurance includes different activities such as quality control, quality management, quality standards, quality planning, process standardization and improvement amongst others. The aim of this work is to further investigate the software quality assurance practices of practitioners in Nigeria. While our previous work covered areas on quality planning, adherence to standardized processes and the inherent challenges, this work has been extended to include quality control, software process improvement and international quality standard organization membership. It also makes comparison based on a similar study carried out in Turkey. The goal is to generate more robust findings that can properly support decision making by the software community. The qualitative research approach, specifically, the use of questionnaire research instruments was applied to acquire data from software practitioners. Results: In addition to the previous results, it was observed that quality assurance practices are quite neglected and this can be the cause of low patronage. Moreover, software practitioners are neither aware of international standards organizations or the required process improvement techniques; as such their claimed standards are not aligned to those of accredited bodies, and are only limited to their local experience and knowledge, which makes it questionable. The comparison with Turkey also yielded similar findings, making the results typical of developing countries. The research instrument used was tested for internal consistency using the Cronbach's alpha, and it was proved reliable. Conclusion: For the software industry in developing countries to grow strong and be a viable source of external revenue, software assurance practices have to be taken seriously because its effect is evident in the final product. Moreover, quality frameworks and tools which require minimum time and cost are highly needed in these countries.Article Citation - WoS: 6Citation - Scopus: 9Experimental Simulation-Based Performance Evaluation of an Sms-Based Emergency Geolocation Notification System(Hindawi Ltd, 2017) Osebor, Isibor; Misra, Sanjay; Omoregbe, Nicholas; Adewumi, Adewole; Fernandez-Sanz, LuisIn an emergency, a prompt response can save the lives of victims. This statement generates an imperative issue in emergency medical services (EMS). Designing a system that brings simplicity in locating emergency scenes is a step towards improving response time. This paper therefore implemented and evaluated the performance of an SMS-based emergency geolocation notification system with emphasis on its SMS delivery time and the system's geolocation and dispatch time. Using the RAS metrics recommended by IEEE for evaluation, the designed system was found to be efficient and effective as its reliability stood within 62.7% to 70.0% while its availability stood at 99% with a downtime of 3.65 days/year.Article Citation - WoS: 8Citation - Scopus: 18Featuring Cio: Roles, Skills and Soft Skills(Igi Global, 2013) Cano, Carmen; Fernandez-Sanz, Luis; Misra, SanjayThis paper describes how the CIO (Chief Information Officer) position appears as a key role in the organizations and the requirements for candidates. The authors compare the requirements presented in different studies to know what are the most important skills for a successful performance as a CIO. They stress the importance of non technical skills as key factors for professional performance. The authors have compared soft skills for CIO or equivalent positions and other professional profiles like programmers or analysts using data taken from thousands of job ads. An overview of the most valuable skills (especially soft skills) for CIOS is presented.Article Citation - WoS: 20Citation - Scopus: 25A Study on the Key Soft Skills for Successful Participation of Students in Multinational Engineering Education(Tempus Publications, 2017) Fernandez-Sanz, Luis; Teresa Villalba, Maria; Amelio Medina, Jose; Misra, Sanjay; Villalba, Maria Teresa; Medina, José Amelio; Computer EngineeringSoft-skills have proved to be a necessary complement to technical skills in today's multinational workplaces. As universities are facing the challenge of promoting internationalization and mobility in students and teachers, they have to decide how to help their students in developing these skills as well as increase their awareness on the cultural differences in multinational settings. After a long trajectory of participation in multinational educational experiences, the authors launched a survey to check if their previous findings on the preferred soft skills by educational experts and managers still remain valid after 5 years. Another goal of the study was the analysis of the link between preference for specific soft skills and cultural background in each country as characterized by Hofstede's indicators. The data collected from 123 experts from 45 different countries have confirmed the existence of a stable core set of preferred soft skills at global level and also for European countries. Results have also shown links between specific cultural indicators and preference for some soft skills.Article Citation - WoS: 33Citation - Scopus: 51Optimizing Green Computing Awareness for Environmental Sustainability and Economic Security as a Stochastic Optimization Problem(Mdpi, 2017) Okewu, Emmanuel; Misra, Sanjay; Maskeliunas, Rytis; Damasevicius, Robertas; Fernandez-Sanz, LuisThe role of automation in sustainable development is not in doubt. Computerization in particular has permeated every facet of human endeavour, enhancing the provision of information for decision-making that reduces cost of operation, promotes productivity and socioeconomic prosperity and cohesion. Hence, a new field called information and communication technology for development (ICT4D) has emerged. Nonetheless, the need to ensure environmentally friendly computing has led to this research study with particular focus on green computing in Africa. This is against the backdrop that the continent is feared to suffer most from the vulnerability of climate change and the impact of environmental risk. Using Nigeria as a test case, this paper gauges the green computing awareness level of Africans via sample survey. It also attempts to institutionalize green computing maturity model with a view to optimizing the level of citizens awareness amid inherent uncertainties like low bandwidth, poor network and erratic power in an emerging African market. Consequently, we classified the problem as a stochastic optimization problem and applied metaheuristic search algorithm to determine the best sensitization strategy. Although there are alternative ways of promoting green computing education, the metaheuristic search we conducted indicated that an online real-time solution that not only drives but preserves timely conversations on electronic waste (e-waste) management and energy saving techniques among the citizenry is cutting edge. The authors therefore reviewed literature, gathered requirements, modelled the proposed solution using Universal Modelling Language (UML) and developed a prototype. The proposed solution is a web-based multi-tier e-Green computing system that educates computer users on innovative techniques of managing computers and accessories in an environmentally friendly way. We found out that such a real-time web-based interactive forum does not only stimulate the interest of the common man in environment-related issues, but also raises awareness about the impact his computer-related activities have on mother earth. This way, he willingly becomes part of the solution to environment degradation in his circle of influence.Review Citation - WoS: 22Citation - Scopus: 39Cybersecurity Deep: Approaches, Attacks Dataset, and Comparative Study(Taylor & Francis inc, 2022) Barik, Kousik; Misra, Sanjay; Konar, Karabi; Fernandez-Sanz, Luis; Murat, Koyuncu; Koyuncu, MuratCyber attacks are increasing rapidly due to advanced digital technologies used by hackers. In addition, cybercriminals are conducting cyber attacks, making cyber security a rapidly growing field. Although machine learning techniques worked well in solving large-scale cybersecurity problems, an emerging concept of deep learning (DL) that caught on during this period caused information security specialists to improvise the result. The deep learning techniques analyzed in this study are convolution neural networks, recurrent neural networks, and deep neural networks in the context of cybersecurity.A framework is proposed, and a real-time laboratory setup is performed to capture network packets and examine this captured data using various DL techniques. A comparable interpretation is presented under the DL techniques with essential parameters, particularly accuracy, false alarm rate, precision, and detection rate. The DL techniques experimental output projects improvise the performance of various real-time cybersecurity applications on a real-time dataset. CNN model provides the highest accuracy of 98.64% with a precision of 98% with binary class. The RNN model offers the second-highest accuracy of 97.75%. CNN model provides the highest accuracy of 98.42 with multiclass class. The study shows that DL techniques can be effectively used in cybersecurity applications. Future research areas are being elaborated, including the potential research topics to improve several DL methodologies for cybersecurity applications.Article Citation - WoS: 36Citation - Scopus: 58A Suite of Object Oriented Cognitive Complexity Metrics(Ieee-inst Electrical Electronics Engineers inc, 2018) Misra, Sanjay; Adewumi, Adewole; Fernandez-Sanz, Luis; Damasevicius, RobertasObject orientation has gained a wide adoption in the software development community. To this end, different metrics that can be utilized in measuring and improving the quality of object-oriented (OO) software have been proposed, by providing insight into the maintainability and reliability of the system. Some of these software metrics are based on cognitive weight and are referred to as cognitive complexity metrics. It is our objective in this paper to present a suite of cognitive complexity metrics that can be used to evaluate OO software projects. The present suite of metrics includes method complexity, message complexity, attribute complexity, weighted class complexity, and code complexity. The metrics suite was evaluated theoretically using measurement theory and Weyuker's properties, practically using Kaner's framework and empirically using thirty projects.Article Citation - WoS: 7Citation - Scopus: 13An Expert System for the Diagnosis of Sexually Transmitted Diseases - Esstd(Ios Press, 2017) Thompson, Temitope; Sowunmi, Olaperi; Misra, Sanjay; Fernandez-Sanz, Luis; Crawford, Broderick; Soto, RicardoOver 93 million people get ill with sexually transmitted diseases in sub-Saharan Africa. However, research has shown that people with sexually transmitted diseases find it difficult to share their problem with a physician due to societal discrimination in Africa. Due to this problem, we have implemented a medical expert system for diagnosing sexually transmitted diseases (ESSTD) that maintains the anonymity of the individuals. The patients diagnose themselves by answering questions provided by the system. This paper presents the design and development of the system. Forward chaining rules were used to implement the knowledge base and the system is easily accessible on mobile platforms. The Java Expert System Shell was used for its inference engine and the system was validated by domain experts. It is useful because it helps to maintain anonymity for patients with STD.Article Citation - WoS: 7Citation - Scopus: 8Automated Recovery and Visualization of Test-To Traceability (tct) Links: an Evaluation(Ieee-inst Electrical Electronics Engineers inc, 2021) Aljawabrah, Nadera; Gergely, Tamas; Misra, Sanjay; Fernandez-Sanz, LuisIn the software development process, traceability links between unit tests and code are not explicitly maintained, and dependencies in most cases are manually identified. As a result, a large amount of effort and time is required during the comprehension process to establish the links between these artifacts. Although there are several methods that can infer such links based on different phenomenons, these methods usually produce different set of traceability links. This work expands upon previous traceability link recovery and visualization studies by implementing a combination of traceability recovery methods that automatically retrieve the links, and visualizing them to help developers to overview the links inferred by various recovery techniques, and also to select the right relations for analyses. The results of the usability study show that the visualization model presented herein can effectively support browsing, comprehension, and maintenance of Test-to Code Traceability (TCT) links in a system with enhanced efficiency, as well as visualization of TCT links from multiple sources is better than a visualization of single source of traceability links.Article Citation - WoS: 2Multi-Paradigm Metric and Its Applicability on Java Projects(Budapest Tech, 2013) Misra, Sanjay; Cafer, Ferid; Akman, Ibahim; Fernandez-Sanz, LuisJAVA is one of the favorite languages amongst software developers. However, the numbers of specific software metrics to evaluate the JAVA code are limited In this paper, we evaluate the applicability of a recently developed multi paradigm metric to JAVA projects. The experimentations show that the Multi paradigm metric is an effective measure for estimating the complexity of the JAVA code/projects, and therefore it can be used for controlling the quality of the projects. We have also evaluated the multi-paradigm metric against the principles of measurement theory.
- «
- 1 (current)
- 2
- 3
- »

