Gökçay, Erhan
Loading...
Profile URL
Name Variants
Gokcay, E
E.,Gökçay
Gökçay,E.
E., Gökçay
G.,Erhan
Gokcay E.
Goekcay, Erhan
Gokcay, Erhan
Erhan, Gokcay
Gökçay, Erhan
E., Gokcay
GOKCAY, E
Erhan, Gökçay
Gokcay,E.
Gökçay E.
G., Erhan
E.,Gokcay
E.,Gökçay
Gökçay,E.
E., Gökçay
G.,Erhan
Gokcay E.
Goekcay, Erhan
Gokcay, Erhan
Erhan, Gokcay
Gökçay, Erhan
E., Gokcay
GOKCAY, E
Erhan, Gökçay
Gokcay,E.
Gökçay E.
G., Erhan
E.,Gokcay
Job Title
Doktor Öğretim Üyesi
Email Address
erhan.gokcay@atilim.edu.tr
Main Affiliation
Software Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
2
ZERO HUNGER

0
Research Products
14
LIFE BELOW WATER

0
Research Products
17
PARTNERSHIPS FOR THE GOALS

0
Research Products
5
GENDER EQUALITY

0
Research Products
16
PEACE, JUSTICE AND STRONG INSTITUTIONS

0
Research Products
8
DECENT WORK AND ECONOMIC GROWTH

0
Research Products
4
QUALITY EDUCATION

0
Research Products
6
CLEAN WATER AND SANITATION

0
Research Products
7
AFFORDABLE AND CLEAN ENERGY

0
Research Products
10
REDUCED INEQUALITIES

0
Research Products
11
SUSTAINABLE CITIES AND COMMUNITIES

0
Research Products
9
INDUSTRY, INNOVATION AND INFRASTRUCTURE

1
Research Products
1
NO POVERTY

0
Research Products
3
GOOD HEALTH AND WELL-BEING

1
Research Products
12
RESPONSIBLE CONSUMPTION AND PRODUCTION

0
Research Products
13
CLIMATE ACTION

0
Research Products
15
LIFE ON LAND

0
Research Products

Documents
16
Citations
395
h-index
7

Documents
15
Citations
293

Scholarly Output
20
Articles
6
Views / Downloads
1/0
Supervised MSc Theses
5
Supervised PhD Theses
2
WoS Citation Count
36
Scopus Citation Count
52
WoS h-index
3
Scopus h-index
3
Patents
0
Projects
0
WoS Citations per Publication
1.80
Scopus Citations per Publication
2.60
Open Access Source
4
Supervised Theses
7
Google Analytics Visitor Traffic
| Journal | Count |
|---|---|
| Multimedia Tools and Applications | 3 |
| 2017 IEEE 1st Ukraine Conference on Electrical and Computer Engineering, UKRCON 2017 - Proceedings -- 1st IEEE Ukraine Conference on Electrical and Computer Engineering, UKRCON 2017 -- 29 May 2017 through 2 June 2017 -- Kyiv -- 131763 | 1 |
| 24th IEEE International Conference on Electronics, Circuits and Systems (ICECS) -- DEC 05-08, 2017 -- Batumi, GEORGIA | 1 |
| 7th International Conference on Cloud Computing and Services Science (CLOSER) -- APR 24-26, 2017 -- Porto, PORTUGAL | 1 |
| 8th International Conference on Cloud Computing and Services Science (CLOSER) -- MAR 19-21, 2018 -- Funchal, PORTUGAL | 1 |
Current Page: 1 / 3
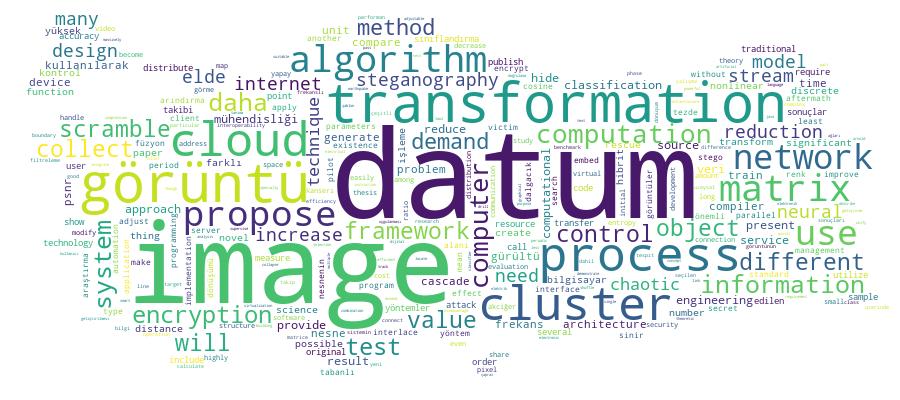
Competency Cloud