Şengül, Gökhan
Loading...
Profile URL
Name Variants
Gokhan, Sengul
Sengul, Gokhan
Sengul,G.
Gökhan, Şengül
Engul G.
Şengül G.
Şengül, Gökhan
G.,Sengul
Sengul, G.
S.,Gokhan
Sengul G.
Ş., Gökhan
G.,Şengül
G., Sengul
Şengül,G.
G., Şengül
S., Gokhan
Ş.,Gökhan
Sengul, Gokhan
Sengul,G.
Gökhan, Şengül
Engul G.
Şengül G.
Şengül, Gökhan
G.,Sengul
Sengul, G.
S.,Gokhan
Sengul G.
Ş., Gökhan
G.,Şengül
G., Sengul
Şengül,G.
G., Şengül
S., Gokhan
Ş.,Gökhan
Job Title
Profesor Doktor
Email Address
gokhan.sengul@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
0
Research Products
 2
2ZERO HUNGER
0
Research Products
 3
3GOOD HEALTH AND WELL-BEING
4
Research Products
 4
4QUALITY EDUCATION
1
Research Products
 5
5GENDER EQUALITY
1
Research Products
 6
6CLEAN WATER AND SANITATION
0
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
1
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
0
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
2
Research Products
 10
10REDUCED INEQUALITIES
0
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
0
Research Products
 13
13CLIMATE ACTION
0
Research Products
 14
14LIFE BELOW WATER
1
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
1
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
0
Research Products

Documents
40
Citations
343
h-index
12

Documents
17
Citations
105

Scholarly Output
83
Articles
49
Views / Downloads
104/171
Supervised MSc Theses
9
Supervised PhD Theses
3
WoS Citation Count
216
Scopus Citation Count
331
Patents
0
Projects
0
WoS Citations per Publication
2.60
Scopus Citations per Publication
3.99
Open Access Source
18
Supervised Theses
12
| Journal | Count |
|---|---|
| Biomedical Research (India) | 5 |
| UBMK 2018 - 3rd International Conference on Computer Science and Engineering -- 3rd International Conference on Computer Science and Engineering, UBMK 2018 -- 20 September 2018 through 23 September 2018 -- Sarajevo -- 143560 | 4 |
| 3rd International Conference on Computer Science and Engineering (UBMK) -- SEP 20-23, 2018 -- Sarajevo, BOSNIA & HERCEG | 2 |
| 2016 24th Signal Processing and Communication Application Conference, SIU 2016 - Proceedings -- 24th Signal Processing and Communication Application Conference, SIU 2016 -- 16 May 2016 through 19 May 2016 -- Zonguldak -- 122605 | 2 |
| International Journal of Engineering Education | 2 |
Current Page: 1 / 9
Scopus Quartile Distribution
Competency Cloud
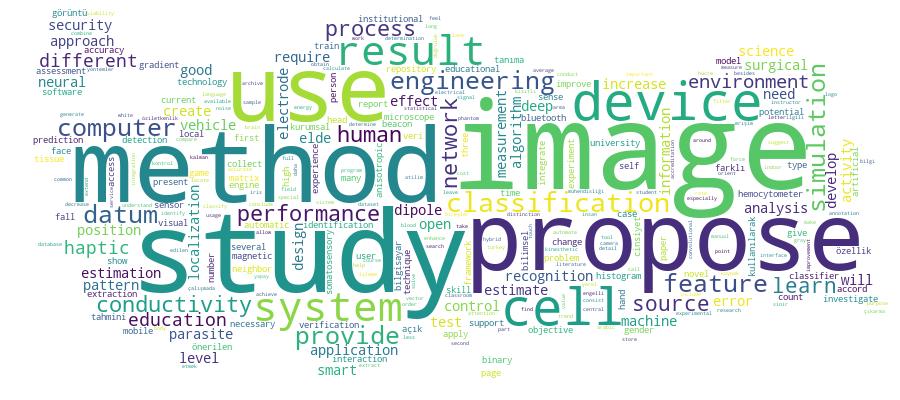
11 results
Scholarly Output Search Results
Now showing 1 - 10 of 11
Conference Object Citation - WoS: 1An Undergraduate Curriculum for Deep Learning(Ieee, 2018) Tirkes, Guzin; Ekin, Cansu Cigdem; Sengul, Gokhan; Bostan, Atila; Karakaya, MuratDeep Learning (DL) is an interesting and rapidly developing field of research which has been currently utilized as a part of industry and in many disciplines to address a wide range of problems, from image classification, computer vision, video games, bioinformatics, and handwriting recognition to machine translation. The starting point of this study is the recognition of a big gap between the sector need of specialists in DL technology and the lack of sufficient education provided by the universities. Higher education institutions are the best environment to provide this expertise to the students. However, currently most universities do not provide specifically designed DL courses to their students. Thus, the main objective of this study is to design a novel curriculum including two courses to facilitate teaching and learning of DL topic. The proposed curriculum will enable students to solve real-world problems by applying DL approaches and gain necessary background to adapt their knowledge to more advanced, industry-specific fields.Article Unidirectional Data Transfer: a Secure System To Push the Data From a High Security Network To a Lower One Over an Actual Air-Gap(International Journal of Scientific Research in Information Systems and Engineering, 2017) Şengül, Gökhan; Bostan, Atila; Karakaya, MuratThe term “air-gap” is typically used to refer physical and logical separation of two computer networks. This type of a separation is generally preferred when the security levels of the networks are not identical. Although the security requirements entail parting the data networks, there is a growing need for fast and automatic transfer of data especially from high-security networks to low-security ones. To protect security sensitive system from the risks originating from low-security network, unidirectional connections that permit the data transfer only from high to low-security network, namely information-diodes, are in use. Nonetheless, each diode solution has its drawbacks either in performance or security viewpoints. In this study, we present a unidirectional data transfer system in which the primary focus is data and signal security in technical design and with a plausible and adaptable data transfer performance. Such that the networks do not touch each other either in physically or logically and the transfer is guaranteed to be unidirectional. Apart from avoiding the malicious transmissions from low to high-security network, we claim that the proposed data diode design is safe from emanation leakage with respect to the contemporary sniffing and spoofing techniques.Article Citation - WoS: 50Citation - Scopus: 70Deep Learning Based Fall Detection Using Smartwatches for Healthcare Applications(Elsevier Sci Ltd, 2022) Sengul, Gokhan; Karakaya, Murat; Misra, Sanjay; Abayomi-Alli, Olusola O.; Damasevicius, RobertasWe implement a smart watch-based system to predict fall detection. We differentiate fall detection from four common daily activities: sitting, squatting, running, and walking. Moreover, we separate falling into falling from a chair and falling from a standing position. We develop a mobile application that collects the acceleration and gyroscope sensor data and transfers them to the cloud. In the cloud, we implement a deep learning algorithm to classify the activity according to the given classes. To increase the number of data samples available for training, we use the Bica cubic Hermite interpolation, which allows us to improve the accuracy of the neural network. The 38 statistical data features were calculated using the rolling update approach and used as input to the classifier. For activity classification, we have adopted the bi-directional long short-term memory (BiLSTM) neural network. The results demonstrate that our system can detect falling with an accuracy of 99.59% (using leave-one-activityout cross-validation) and 97.35% (using leave-one-subject-out cross-validation) considering all activities. When considering only binary classification (falling vs. all other activities), perfect accuracy is achieved.Conference Object Deep Learning and Current Trends in Machine Learning(Ieee, 2018) Bostan, Atila; Sengul, Gokhan; Tirkes, Guzin; Ekin, Cansu; Karakaya, MuratAcademic interest and commercial attention can be used to identify how much potential a novel technology may have. Since the prospective advantages in it may help solving some problems that are not solved yet or improving the performance of readily available ones. In this study, we have investigated the Web of Science (WOS) indexing service database for the publications on Deep Learning (DL), Machine Learning (ML), Convolutional Neural Networks (CNN), and Image Processing to reveal out the current trend. The figures indicate the strong potential in DL approach especially in image processing domain.Article A Wireless Control System Based on Smart Bluetooth and Ibeacon Technology for Auditing the Patrols(International Journal of Scientific Research in Information Systems and Engineering, 2016) Karakaya, Murat; Şengül, Gökhan; Bostan, AtilaPatrol systems are used as a method of ensuring security and protection of large areas and facilities such as university campuses, military zones, etc. In general, security personnel assigned to the patrol system visit the pre-determined checkpoints at regular intervals and are obliged to make the safety control of these locations. Security personnel (guards) are also audited to check if they covered all the essential control points on time or not. In recent years, considering energy efficiency, new Bluetooth devices and protocols are designed and produced. One of the most popular low-energy Bluetooth protocols is Smart Bluetooth (version 4.0). In this work, we integrated mobile devices (smart phone or tablet) with IBeacons. IBeacons are devices emitting beacons using Smart Bluetooth signals. Since Smart Bluetooth consumes low energy, these devices are small in size, have long life durations and very cheap. In this work, we propose and implement a new system to record the patrol officers’ movements in the subject areas. At the proposed system, IBeacons are first deployed in the monitoring areas. The location and the identification of the deployed IBeacon are stored in a central database. We developed a mobile application for Android devices which can scan the environment for IBeacon signals. The mobile application collects the sensed IBeacon IDs, stamps it with a time tag and uploads it along with the mobile device ID to the central database. Using these records, we can monitor the movements of the security guards. We have also developed a web application to generate an executive summary report from these records.Article Determination and Identification of Dangerously Lane Changing Vehicles in Traffic by Image Processing Techniques(International Journal of Scientific Research in Information Systems and Engineering, 2017) Şengül, Gökhan; Karakaya, Murat; Bostan, AtilaDue to increase of vehicle usage all around the world, the importance of safety driving in traffic is increasing. All of the countries around the world are taking actions to increase the safety driving habitats and decrease the number of traffic accidents. One of the applied precautions is to put necessary automatic auditing mechanisms into service for controlling the drivers as they drive since reckless drivers may not obey many traffic rules. In this study, image and video processing based methods are applied to identify the dangerously lane changing vehicles/drivers in the traffic. The proposed method focuses on to detect three different violations in traffic: the vehicles frequently changing traffic lanes, the vehicles changing lanes when it is forbidden, and the vehicles overtaking the other vehicles using the right lanes instead of left one. The proposed method is based on the image and video processing techniques. It first detects the vehicles in video sequences, then tracks the vehicles in the following frames and determines the lane changes of the vehicles. In the vehicle detection phase an image subtraction method is used. In the vehicle tracking phase, Kalman filtering tracking algorithm is used. After determining the lane changes of the vehicles/drivers, a rule based decision system is used to find out the vehicles/drivers improperly changing lanes and those vehicles are marked on the video. The proposed method is tested on the videos captured from real traffic environments and promising results are obtained.Article A Smart Classroom Application: Monitoring and Reporting Attendance Automatically Using Smart Devices(International Journal of Scientific Research in Information Systems and Engineering, 2017) Şengül, Gökhan; Karakaya, Murat; Bostan, AtilaFor recording attendance in a classroom, generally instructors collect signatures of the attendees. Then, at the end of the semester, those signatures need to be counted and reported. This process causes waste of time and effort for both instructors and attendees. Besides this process is very error prone. Moreover, in crowded classes, there could be some misuses of this process. In this study, a smart classroom application is proposed and developed in order to monitor the attendance of the students in a classroom environment. In the design, a low-energy Bluetooth device is located at each classroom. Identification number (ID) of the low-energy Bluetooth device and the name/number of the classroom that the device is located are matched and stored in a central database. In addition to this information, the name of the courses given in that classroom and their time tables are also stored in the central database. Thus, in the database, the weekly course schedule of the classrooms is available. In addition to this central database infrastructure, a mobile application is developed that can run on both in mobile phones and smart watches. The users first install the application on their own smart devices. Whenever an attendee enters to a classroom, the smart device and its application interacts with the low-energy Bluetooth device. The student’s identification number (Student ID: SID), the identification number (ID) of the low-energy Bluetooth device located at the class, the day and time of the interaction are sent to the central database by the smart device. Using this information, the name of the attendee and the courses that he/she attended are matched using the SID of the attendee, the ID of the low-energy Bluetooth device, the day and time of the interaction. Those matching information are also stored in the central database. The records in the central database are used to create any automatic reports, i.e. the attendance status, the time and duration of the attendance, and the classroom (course) of the record. The advantage of the proposed system is that it is a fully automatic system that records the presence of the students, generates automatic attendance reports, does not require any extra device except installing a mobile application onto smart phones or smart watches of the student, and can be deployed with a low budget. The proposed system is tested in real classroom environment and it is proven to be operational.Conference Object An Iot Application for Locating Victims Aftermath of an Earthquake(Ieee, 2017) Karakaya, Murat; Sengul, Gokhan; Gokcay, ErhanThis paper presents an Internet of Things (IoT) framework which is specially designed for assisting the research and rescue operations targeted to collapsed buildings aftermath of an earthquake. In general, an IoT network is used to collect and process data from different sources called things. According to the collected data, an IoT system can actuate different mechanisms to react the environment. In the problem at hand, we exploit the IoT capabilities to collect the data about the victims before the building collapses and when it falls down the collected data is processed to generate useful reports which will direct the search and rescue efforts. The proposed framework is tested by a pilot implementation with some simplifications. The initial results and experiences are promising. During the pilot implementation, we observed some issues which are addressed in the proposed IoT framework properly.Article Biometric Verification on E-Id Secure Access Devices: a Case Study on Turkish National E-Id Card Secure Access Device Specifications(International Journal of Information Security Science, 2017) Bostan, Atila; Şengül, Gökhan; Karakaya, MuratBiometric verification on e-ID cards requires clear procedures and standards be defined, especially when the access devices are anticipated to be produced commercial companies. Turkish national e-ID card project has reached the dissemination step. Now the commercial companies are expected to produce and market e-ID card access devices which will conduct secure electronic identity verification functions. However, published standards specifying e-ID card-access-device requirements are ambiguous on biometric verification procedures. In this study, we intended to attract scientific interest to the problems identified in the current design of biometric verification on Turkish national e-ID cards and proposed several verification alternatives which enables the production of e-ID card access devices in a commercial-competition environment.Article Using Bluetooth Low Energy Beacons for Indoor Localization(International Journal of Intelligent Systems and Applications in Engineering, 2017) Şengül, Gökhan; Karakaya, MuratBluetooth Low Energy (BLE) Beacons gain high popularity due to their low consumption of energy and, thereby, long lifetime. Using the BLE protocol, these devices emit advertisement packets at fixed intervals for a short duration. Indoor localization solutions aim to provide an accurate, low cost estimate of sub-room indoor positioning. There are various techniques proposed for this purpose. BLE Beacons are good hardware candidates to assist the creation of such indoor localization solutions. Given the exact position of BLE Beacons, one can attempt to estimate a receiver position according to the received signal power. In this work, we investigated the success of such an indoor localization approach employing multiple BLE Beacons and two different estimation techniques. The results of the experiments indicate that employing multiple BLE Beacons increases the success of prediction techniques considerably.

