Çulha, Davut
Loading...
Profile URL
Name Variants
Çulha, Dr. Davut
Davut, Culha
Davut, Çulha
D., Culha
Ç.,Davut
D.,Çulha
Çulha,D.
Culha D.
Ç., Davut
Culha, Davut
D., Çulha
C.,Davut
Çulha, Davut
D.,Culha
Culha,D.
C., Davut
Davut, Culha
Davut, Çulha
D., Culha
Ç.,Davut
D.,Çulha
Çulha,D.
Culha D.
Ç., Davut
Culha, Davut
D., Çulha
C.,Davut
Çulha, Davut
D.,Culha
Culha,D.
C., Davut
Job Title
Doçent Doktor
Email Address
davut.culha@atilim.edu.tr
Main Affiliation
Software Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
SDG data is not available

Scopus data could not be loaded because of an error. Please refresh the page or try again later.

This researcher does not have a WoS ID.

Scholarly Output
8
Articles
1
Views / Downloads
13/20
Supervised MSc Theses
2
Supervised PhD Theses
0
WoS Citation Count
27
Scopus Citation Count
33
Patents
0
Projects
0
WoS Citations per Publication
3.38
Scopus Citations per Publication
4.13
Open Access Source
1
Supervised Theses
2
| Journal | Count |
|---|---|
| International Congress on Big Data, Deep Learning and Fighting Cyber Terrorism, IBIGDELFT 2018 - Proceedings -- 2018 International Congress on Big Data, Deep Learning and Fighting Cyber Terrorism, IBIGDELFT 2018 -- 3 December 2018 through 4 December 2018 -- Ankara -- 144574 | 2 |
| 2025 7th International Conference on Blockchain Computing and Applications, BCCA 2025 -- 7th International Conference on Blockchain Computing and Applications, BCCA 2025 -- 2025-10-14 Through 2025-10-17 -- Dubrovnik -- 216110 | 1 |
| 6th International Conference on Blockchain Computing and Applications -- NOV 26-29, 2024 -- Zayed University, Dubai, U ARAB EMIRATES | 1 |
| International Congress on Big Data, Deep Learning and Fighting Cyber Terrorism (IBIGDELFT) -- DEC 03-04, 2018 -- Turkish IT Author, Ankara, TURKEY | 1 |
| Journal of Universal Computer Science | 1 |
Current Page: 1 / 1
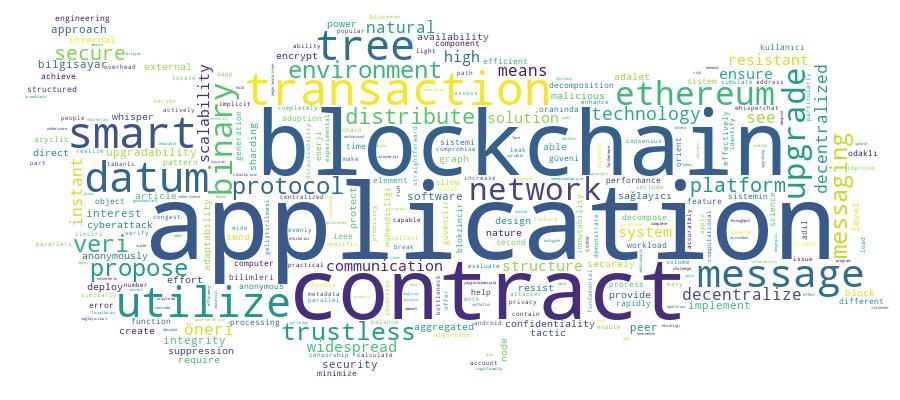
Competency Cloud