Mısra, Sanjay
Loading...

Profile URL
Name Variants
M.,Sanjay
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Job Title
Profesör Doktor
Email Address
sanjay.misra@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
3
Research Products
 2
2ZERO HUNGER
5
Research Products
 3
3GOOD HEALTH AND WELL-BEING
2
Research Products
 4
4QUALITY EDUCATION
6
Research Products
 5
5GENDER EQUALITY
2
Research Products
 6
6CLEAN WATER AND SANITATION
1
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
8
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
11
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
11
Research Products
 10
10REDUCED INEQUALITIES
2
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
3
Research Products
 13
13CLIMATE ACTION
7
Research Products
 14
14LIFE BELOW WATER
10
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
4
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
9
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
199
Articles
133
Views / Downloads
686/271
Supervised MSc Theses
3
Supervised PhD Theses
0
WoS Citation Count
2629
Scopus Citation Count
3894
Patents
0
Projects
0
WoS Citations per Publication
13.21
Scopus Citations per Publication
19.57
Open Access Source
53
Supervised Theses
3
| Journal | Count |
|---|---|
| Acta Polytechnica Hungarica | 12 |
| Tehnicki Vjesnik | 8 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 2011 International Conference on Computational Science and Its Applications, ICCSA 2011 -- 20 June 2011 through 23 June 2011 -- Santander -- 85480 | 5 |
| Journal of Physics: Conference Series -- 3rd International Conference on Computing and Applied Informatics 2018, ICCAI 2018 -- 18 September 2018 through 19 September 2018 -- Medan, Sumatera Utara -- 149865 | 4 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 12th International Conference on Computational Science and Its Applications, ICCSA 2012 -- 18 June 2012 through 21 June 2012 -- Salvador de Bahia -- 90945 | 4 |
Current Page: 1 / 22
Scopus Quartile Distribution
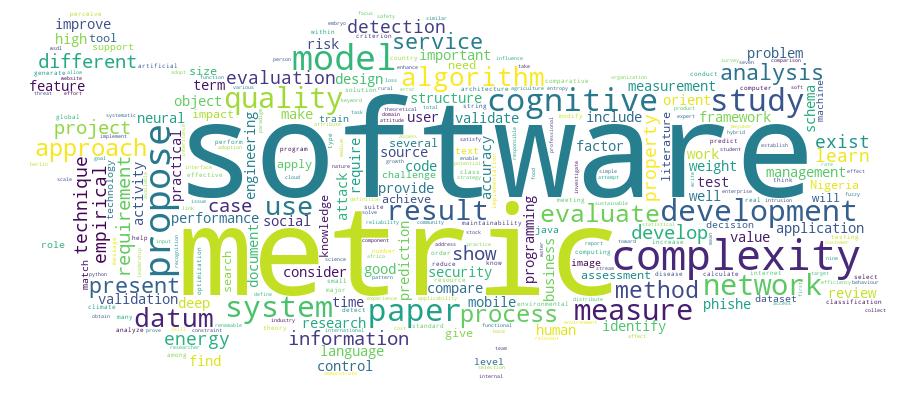
Competency Cloud
7 results
Scholarly Output Search Results
Now showing 1 - 7 of 7
Review Citation - WoS: 3Citation - Scopus: 9An Empirical Evaluation of Software Quality Assurance Practices and Challenges in a Developing Country: a Comparison of Nigeria and Turkey(Springer international Publishing Ag, 2016) Sowunmi, Olaperi Yeside; Mısra, Sanjay; Misra, Sanjay; Fernandez-Sanz, Luis; Crawford, Broderick; Soto, Ricardo; Mısra, Sanjay; Computer Engineering; Computer EngineeringBackground: The importance of quality assurance in the software development process cannot be overemphasized because its adoption results in high reliability and easy maintenance of the software system and other software products. Software quality assurance includes different activities such as quality control, quality management, quality standards, quality planning, process standardization and improvement amongst others. The aim of this work is to further investigate the software quality assurance practices of practitioners in Nigeria. While our previous work covered areas on quality planning, adherence to standardized processes and the inherent challenges, this work has been extended to include quality control, software process improvement and international quality standard organization membership. It also makes comparison based on a similar study carried out in Turkey. The goal is to generate more robust findings that can properly support decision making by the software community. The qualitative research approach, specifically, the use of questionnaire research instruments was applied to acquire data from software practitioners. Results: In addition to the previous results, it was observed that quality assurance practices are quite neglected and this can be the cause of low patronage. Moreover, software practitioners are neither aware of international standards organizations or the required process improvement techniques; as such their claimed standards are not aligned to those of accredited bodies, and are only limited to their local experience and knowledge, which makes it questionable. The comparison with Turkey also yielded similar findings, making the results typical of developing countries. The research instrument used was tested for internal consistency using the Cronbach's alpha, and it was proved reliable. Conclusion: For the software industry in developing countries to grow strong and be a viable source of external revenue, software assurance practices have to be taken seriously because its effect is evident in the final product. Moreover, quality frameworks and tools which require minimum time and cost are highly needed in these countries.Review Citation - WoS: 16Citation - Scopus: 20Assessing the Coverage of E-Health Services in Sub-Saharan Africa a Systematic Review and Analysis(Georg Thieme verlag Kg, 2017) Adeloye, Davies; Adigun, Taiwo; Misra, Sanjay; Omoregbe, NicholasBackground: E-Health has attracted growing interests globally. The relative lack of facilities, skills, funds and information on existing e-Health initiatives has affected progress on e-Health in Africa. Objectives: To review publicly available literature on e-Health in sub-Saharan Africa (sSA) towards providing information on existing and ongoing e-Health initiatives in the region. Methods: Searches of relevant literature were conducted on Medline, EMBASE and Global Health, with search dates set from 1990 to 2016. We included studies on e-Health initiatives (prototypes, designs, or completed projects) targeting population groups in sSA. Results: Our search returned 2322 hits, with 26 studies retained. Included studies were conducted in 14 countries across the four sub-regions in sSA (Central, East, South and West) and spreading over a 12-year period, 2002-2014. Six types of e-Health interventions were reported, with 17 studies (65%) based on telemedicine, followed by mHealth with 5 studies (19%). Other e-Health types include expert system, electronic medical records, e-mails, and online health module. Specific medical specialties covered include dermatology (19%), pathology (12%) and radiology (8%). Successes were 'widely reported' (representing 50% overall acceptance or positive feedbacks in a study) in 10 studies (38%). The prominent challenges reported were technical problems, poor inter net and connectivity, participants' selection biases, contextual issues, and lack of funds. Conclusion: E-Health is evolving in sSA, but with poorly published evidence. While we call for more quality research in the region, it is also important that population-wide policies and on-going e-Health initiatives are contextually feasible, acceptable, and sustainable.Review Citation - WoS: 22Citation - Scopus: 39Cybersecurity Deep: Approaches, Attacks Dataset, and Comparative Study(Taylor & Francis inc, 2022) Barik, Kousik; Misra, Sanjay; Konar, Karabi; Fernandez-Sanz, Luis; Murat, Koyuncu; Koyuncu, MuratCyber attacks are increasing rapidly due to advanced digital technologies used by hackers. In addition, cybercriminals are conducting cyber attacks, making cyber security a rapidly growing field. Although machine learning techniques worked well in solving large-scale cybersecurity problems, an emerging concept of deep learning (DL) that caught on during this period caused information security specialists to improvise the result. The deep learning techniques analyzed in this study are convolution neural networks, recurrent neural networks, and deep neural networks in the context of cybersecurity.A framework is proposed, and a real-time laboratory setup is performed to capture network packets and examine this captured data using various DL techniques. A comparable interpretation is presented under the DL techniques with essential parameters, particularly accuracy, false alarm rate, precision, and detection rate. The DL techniques experimental output projects improvise the performance of various real-time cybersecurity applications on a real-time dataset. CNN model provides the highest accuracy of 98.64% with a precision of 98% with binary class. The RNN model offers the second-highest accuracy of 97.75%. CNN model provides the highest accuracy of 98.42 with multiclass class. The study shows that DL techniques can be effectively used in cybersecurity applications. Future research areas are being elaborated, including the potential research topics to improve several DL methodologies for cybersecurity applications.Review A Study of Existing Use Case Extensions and Experience: a Systematic Review(Taylor & Francis Ltd, 2020) Arogundade, Oluwasefunmi'Tale; Olotu, Samuel Ibukun; Abayomi-Alli, Olusola; Misra, Sanjay; Ikotun, Abiodun MotunrayoUse case has embedded potentials that enable the diversity in its adoption to addressing other issues in software engineering. This objective of this paper is to gathered and classified use case researches carried out over the years and defines the state-of-art. We identified and analysed 62 relevant articles with deep insights into six different initiatives. The publications included 29 journal articles, 18 conference articles, 3 reports, 5 book chapters, 5 workshops and 2 symposiums. This study deduced that as many as 15 different extensions are proposed from use case ranging from formal descriptions to subjective methodology. Use case has evolved from initial functional requirement elicitation to a more formal and extensive structure. There are fewer publications in cloud computing and use case-based systems. This study contributed to the use case body of knowledge by assessing the extended initiatives and giving an overview of the challenges that are not yet resolved.Review Citation - Scopus: 11A Discussion on Assuring Software Quality in Small and Medium Software Enterprises: an Empirical Investigation;(2011) Tolga Pusatli,O.; Misra,S.Under the studies of general core activities including software inspection, review and testing to achieve quality objectives in small-medium size enterprises (SMEs), the paper presents a contemporary view of such companies against quality measures. The results from a local empirical investigation of quality standards in the Turkish software industry are reported. Around 150 software companies have been approached from which 17 detailed feedback inform that in order to ensure software quality, standards including internationally recognized International Standards Organization (ISO) and Capability Maturity Model Integration (CMMI) are given credit. However the substantial workload and resources required to obtain them are also reported as serious; downscaled frameworks of such large models proposed in the literature are not well known by the SMEs either. The paper also discusses work around that bypasses such standards to ease delivery of products while keeping certificates as labels just to acquire new jobs for the business.Review Citation - WoS: 17Citation - Scopus: 28A Systematic Literature Review on Compliance Requirements Management of Business Processes(Springer india, 2020) Mustapha, A. M.; Arogundade, O. T.; Misra, Sanjay; Damasevicius, Robertas; Maskeliunas, RytisOne crucial aspect that had cost business organizations so much is management of compliance requirements from various regulatory sources. In a bid to avoid being penalized, some organizations have adopted various techniques to accomplish this task. However, literature revealed that few thorough reviews have been centered on this subject in a systematic way. This implies that a review that systematically captured the entire crucial elements such as implementation environment, constraints types addressed, main contributions and strengths of the existing techniques is missing. This has led to the lack of sufficiently good context of operation. A systematic review on existing literatures is presented in this paper, which focuses on the management of business process compliance requirements in order to present summarized evidences and provide a lead-up for appropriately positioning new research activities. The guideline for conducting systematic literature review in software engineering by Kitchenham was employed in carrying out the systematic review as well as a review planning template to execute the review. Results showed that control flow and data flow requirements have been addressed most in recent time. The temporal and resource allocation requirements have been under researched. The approaches that have been employed in business process compliance requirements management are model checking, patterns, semantic, formal, ontology, goal-based requirements analysis and network analysis. The traditional business environment has been put into consideration more than the cloud environment. The summary of research contributions revealed that the approaches have been more of formal techniques compared to model checking and semantics. This shows that there is a need for more research on business process compliance that will be centered on the cloud environment. Researchers will be able to suggest the technique to be adopted based on the combined importance of each criterion that was defined in this work.Review Citation - WoS: 31Citation - Scopus: 43A Systematic Literature Review of Open Source Software Quality Assessment Models(Springer international Publishing Ag, 2016) Adewumi, Adewole; Misra, Sanjay; Omoregbe, Nicholas; Crawford, Broderick; Soto, RicardoBackground: Many open source software (OSS) quality assessment models are proposed and available in the literature. However, there is little or no adoption of these models in practice. In order to guide the formulation of newer models so they can be acceptable by practitioners, there is need for clear discrimination of the existing models based on their specific properties. Based on this, the aim of this study is to perform a systematic literature review to investigate the properties of the existing OSS quality assessment models by classifying them with respect to their quality characteristics, the methodology they use for assessment, and their domain of application so as to guide the formulation and development of newer models. Searches in IEEE Xplore, ACM, Science Direct, Springer and Google Search is performed so as to retrieve all relevant primary studies in this regard. Journal and conference papers between the year 2003 and 2015 were considered since the first known OSS quality model emerged in 2003. Results: A total of 19 OSS quality assessment model papers were selected. To select these models we have developed assessment criteria to evaluate the quality of the existing studies. Quality assessment models are classified into five categories based on the quality characteristics they possess namely: single-attribute, rounded category, community-only attribute, non-community attribute as well as the non-quality in use models. Our study reflects that software selection based on hierarchical structures is found to be the most popular selection method in the existing OSS quality assessment models. Furthermore, we found that majority (47%) of the existing models do not specify any domain of application. Conclusions: In conclusion, our study will be a valuable contribution to the community and helps the quality assessment model developers in formulating newer models and also to the practitioners (software evaluators) in selecting suitable OSS in the midst of alternatives.

