Mısra, Sanjay
Loading...

Profile URL
Name Variants
M.,Sanjay
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Job Title
Profesör Doktor
Email Address
sanjay.misra@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
3
Research Products
 2
2ZERO HUNGER
5
Research Products
 3
3GOOD HEALTH AND WELL-BEING
2
Research Products
 4
4QUALITY EDUCATION
6
Research Products
 5
5GENDER EQUALITY
2
Research Products
 6
6CLEAN WATER AND SANITATION
1
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
8
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
11
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
11
Research Products
 10
10REDUCED INEQUALITIES
2
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
3
Research Products
 13
13CLIMATE ACTION
7
Research Products
 14
14LIFE BELOW WATER
10
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
4
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
9
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
199
Articles
133
Views / Downloads
686/271
Supervised MSc Theses
3
Supervised PhD Theses
0
WoS Citation Count
2629
Scopus Citation Count
3894
Patents
0
Projects
0
WoS Citations per Publication
13.21
Scopus Citations per Publication
19.57
Open Access Source
53
Supervised Theses
3
| Journal | Count |
|---|---|
| Acta Polytechnica Hungarica | 12 |
| Tehnicki Vjesnik | 8 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 2011 International Conference on Computational Science and Its Applications, ICCSA 2011 -- 20 June 2011 through 23 June 2011 -- Santander -- 85480 | 5 |
| Journal of Physics: Conference Series -- 3rd International Conference on Computing and Applied Informatics 2018, ICCAI 2018 -- 18 September 2018 through 19 September 2018 -- Medan, Sumatera Utara -- 149865 | 4 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 12th International Conference on Computational Science and Its Applications, ICCSA 2012 -- 18 June 2012 through 21 June 2012 -- Salvador de Bahia -- 90945 | 4 |
Current Page: 1 / 22
Scopus Quartile Distribution
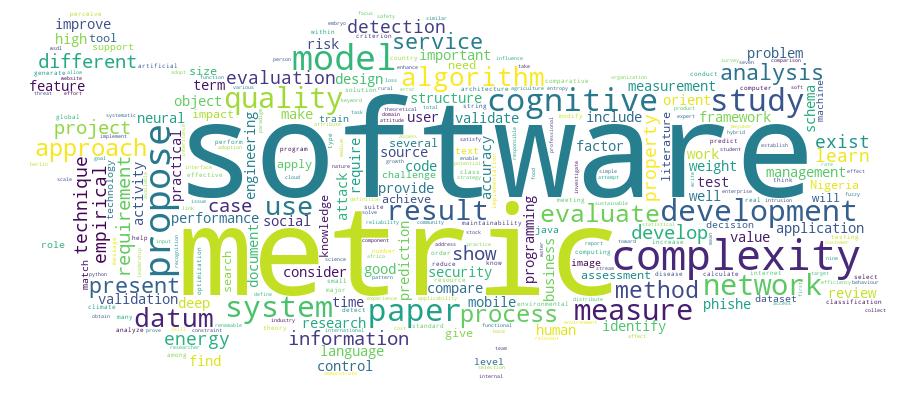
Competency Cloud
39 results
Scholarly Output Search Results
Now showing 1 - 10 of 39
Conference Object Embryo Spatial Model Reconstruction(Springer international Publishing Ag, 2020) Dirvanauskas, Darius; Maskeliunas, Rytis; Raudonis, Vidas; Misra, SanjayTime lapse microscopy offered new solutions to study embryo development process. It allows embryologist to monitor embryo growth in real time and evaluate them without interfering into their growth environment. Embryo evaluation during growth process is one of the key criteria in embryo selection for fertilization. Live embryo monitoring is time consuming and new tools are offered to automate part of process. Our proposed algorithm gives new possibilities for embryo monitoring. It uses embryo images which are taken from different embryo layers, extracts embryo cell features and returns metrical evaluation to compare different embryos. High number of extracted features shows embryo fragmentation. Other tool whichwe present is spatial embryo model. Features extracted from embryo layers are combined together to spatial model. It allows embryologist to examine embryo model and compare different layers in one space. The obtained spatial embryo model will be later used to develop new algorithms for embryo analysis tasks.Article Citation - WoS: 104Citation - Scopus: 163Cassava Disease Recognition From Low-Quality Images Using Enhanced Data Augmentation Model and Deep Learning(Wiley, 2021) Abayomi-Alli, Olusola Oluwakemi; Damasevicius, Robertas; Misra, Sanjay; Maskeliunas, RytisImprovement of deep learning algorithms in smart agriculture is important to support the early detection of plant diseases, thereby improving crop yields. Data acquisition for machine learning applications is an expensive task due to the requirements of expert knowledge and professional equipment. The usability of any application in a real-world setting is often limited by unskilled users and the limitations of devices used for acquiring images for classification. We aim to improve the accuracy of deep learning models on low-quality test images using data augmentation techniques for neural network training. We generate synthetic images with a modified colour value distribution to expand the trainable image colour space and to train the neural network to recognize important colour-based features, which are less sensitive to the deficiencies of low-quality images such as those affected by blurring or motion. This paper introduces a novel image colour histogram transformation technique for generating synthetic images for data augmentation in image classification tasks. The approach is based on the convolution of the Chebyshev orthogonal functions with the probability distribution functions of image colour histograms. To validate our proposed model, we used four methods (resolution down-sampling, Gaussian blurring, motion blur, and overexposure) for reducing image quality from the Cassava leaf disease dataset. The results based on the modified MobileNetV2 neural network showed a statistically significant improvement of cassava leaf disease recognition accuracy on lower-quality testing images when compared with the baseline network. The model can be easily deployed for recognizing and detecting cassava leaf diseases in lower quality images, which is a major factor in practical data acquisition.Article Citation - Scopus: 48Identifying Phishing Attacks in Communication Networks Using Url Consistency Features(Inderscience Publishers, 2020) Azeez,N.A.; Salaudeen,B.B.; Misra,S.; Damasevicius,R.; Maskeliunas,R.Phishing is a fraudulent attempt by cybercriminals, where the target audience is addressed by a text message, phone call or e-mail, requesting classified and sensitive information after presenting himself/herself as a legitimate agent. Successful phishing attack may result into financial loss and identity theft. Identifying forensic characteristics of phishing attack can help to detect the attack and its perpetuators and as well as to enable defence against it. To shield internet users from phishing assaults, numerous anti-phishing models have been proposed. Currently employed techniques to handle these challenges are not sufficient and capable enough. We aim at identifying phishing sites in order to guard internet users from being vulnerable to any form of phishing attacks by verifying the conceptual and literal consistency between the uniform resource locator (URL) and the web content. The implementation of the proposed PhishDetect method achieves an accuracy of 99.1%; indicating that it is effective in detecting various forms of phishing attacks. © 2020 Inderscience Enterprises Ltd.. All rights reserved.Article Citation - WoS: 25Identifying Phishing Attacks in Communication Networks Using Url Consistency Features(inderscience Enterprises Ltd, 2020) Azeez, Nureni Ayofe; Salaudeen, Balikis Bolanle; Misra, Sanjay; Damasevicius, Robertas; Maskeliunas, RytisPhishing is a fraudulent attempt by cybercriminals, where the target audience is addressed by a text message, phone call or e-mail, requesting classified and sensitive information after presenting himself/herself as a legitimate agent. Successful phishing attack may result into financial loss and identity theft. Identifying forensic characteristics of phishing attack can help to detect the attack and its perpetuators and as well as to enable defence against it. To shield internet users from phishing assaults, numerous anti-phishing models have been proposed. Currently employed techniques to handle these challenges are not sufficient and capable enough. We aim at identifying phishing sites in order to guard internet users from being vulnerable to any form of phishing attacks by verifying the conceptual and literal consistency between the uniform resource locator (URL) and the web content. The implementation of the proposed PhishDetect method achieves an accuracy of 99.1%; indicating that it is effective in detecting various forms of phishing attacks.Article Citation - Scopus: 1Optimizing the Stochastic Deployment of Small Base Stations in an Interleave Division Multiple Access-Based Heterogeneous Cellular Networks(Wiley, 2022) Noma-Osaghae, Etinosa; Misra, Sanjay; Koyuncu, MuratThe use of small base stations (SBSs) to improve the throughput of cellular networks gave rise to the advent of heterogeneous cellular networks (HCNs). Still, the interleave division multiple access (IDMA) performance in sleep mode active HCNs has not been studied in the existing literature. This research examines the 24-h throughput, spectral efficiency (SE), and energy efficiency (EE) of an IDMA-based HCN and compares the result with orthogonal frequency division multiple access (OFDMA). An energy-spectral-efficiency (ESE) model of a two-tier HCN was developed. A weighted sum modified particle swarm optimization (PSO) algorithm simultaneously maximized the SE and EE of the IDMA-based HCN. The result obtained showed that the IDMA performs at least 68% better than the OFDMA on the throughput metric. The result also showed that the particle swarm optimization algorithm produced the Pareto optimal front at moderate traffic levels for all varied network parameters of SINR threshold, SBS density, and sleep mode technique. The IDMA-based HCN can improve the throughput, SE, and EE via sleep mode techniques. Still, the combination of network parameters that simultaneously maximize the SE and EE is interference limited. In sleep mode, the performance of the HCN is better if the SBSs can adapt to spatial and temporal variations in network traffic.Article Citation - WoS: 36Agriculture 4.0: an Implementation Framework for Food Security Attainment in Nigeria's Post-Covid Era(Ieee-inst Electrical Electronics Engineers inc, 2021) Oruma, Samson O.; Misra, Sanjay; Fernandez-Sanz, LuisThe challenge of Nigeria's food insecurity in the era of the Covid-19 pandemic, insecurity, climate change, population growth, food wastage, etc., is a demanding task. This study addresses Nigeria's food insecurity challenges by adopting agriculture 4.0 and commercial farming. Using data from six digital libraries, the Nigerian Bureau of Statistics, and other internet sources, we conducted a Systematic Literature Review (SLR using PRISMA) on Nigeria's agriculture, food security, and agriculture 4.0. Our results show Nigeria's current agricultural state, threats to food security, and modern digital agriculture technologies. We adapted our SLR findings to develop an implementation framework for agriculture 4.0 in solving Nigeria's food insecurity challenge in the post-Covid-19 era. Our proposed framework integrates precision agriculture in Nigeria's food production and the necessary enabling digital technologies in the agri-food supply chain. We analyzed the critical implementation considerations during each agri-food supply chain stage of farming inputs, farming scale, farming approach, farming operation, food processing, food preservation/storage, distribution/logistics, and the final consumers. This study will help researchers, investors, and the government address food security in Nigeria. The implementation of agriculture 4.0 will substantially contribute to SDG 2 (zero hunger), SDG 3 (good health and well-being), and SDG 8 (decent work and economic growth) of #Envision 2030 of the United Nations, for the benefit of Nigeria, Africa, and the entire world.Article Citation - WoS: 10Citation - Scopus: 18An Ontology-Based Information Extraction System for Organic Farming(Igi Global, 2021) Abayomi-Alli, Adebayo Adewumi; Arogundade, Oluwasefunmi 'Tale; Misra, Sanjay; Akala, Mulkah Opeyemi; Ikotun, Abiodun Motunrayo; Ojokoh, Bolanle AdefowokeIn the existing farming system, information is obtained manually, and most times, farmers act based on their discretion. Sometimes, farmers rely on information from experts and extension officers for decision making. In recent times, a lot of information systems are available with relevant information on organic farming practices; however, such information is scattered in different context, form, and media all over the internet, making their retrieval difficult. The use of ontology with the aid of a conceptual scheme makes the comprehensive and detailed formalization of any subject domain possible. This study is aimed at acquiring, storing, and providing organic farming-based information available to current and intending software developer who may wish to develop applications for farmers. It employs information extraction (IE) and ontology development techniques to develop an ontology-based information extraction (OBIE) system called ontology-based information extraction system for organic farming (OBIESOF). The knowledge base was built using protege editor; Java was used for the implementation of the ontology knowledge base with the aid of the high-level application programming language for working web ontology language application program interface (OWLAPI). In contrast, HermiT was used to checking the consistencies of the ontology and for submitting queries in order to verify their validity. The queries were expressed in description logic (DL) query language. The authors tested the capability of the ontology to respond to user queries by posing instances of the competency questions from DL query interface. The answers generated by the ontology were promising and serve as positive pointers to its usefulness as a knowledge repository.Article Citation - WoS: 3Citation - Scopus: 5Particle Swarm Optimization of the Spectral and Energy Efficiency of an Scma-Based Heterogeneous Cellular Network(Wiley, 2022) Noma-Osaghae, Etinosa; Misra, Sanjay; Ahuja, Ravin; Koyuncu, MuratBackground The effect of stochastic small base station (SBS) deployment on the energy efficiency (EE) and spectral efficiency (SE) of sparse code multiple access (SCMA)-based heterogeneous cellular networks (HCNs) is still mostly unknown. Aim This research study seeks to provide insight into the interaction between SE and EE in SBS sleep-mode enabled SCMA-based HCNs. Methodology A model that characterizes the energy-spectral-efficiency (ESE) of a two-tier SBS sleep-mode enabled SCMA-based HCN was derived. A multiobjective optimization problem was formulated to maximize the SE and EE of the SCMA-based HCN simultaneously. The multiobjective optimization problem was solved using a proposed weighted sum modified particle swarm optimization algorithm (PSO). A comparison was made between the performance of the proposed weighted sum modified PSO algorithm and the genetic algorithm (GA) and the case where the SCMA-based HCN is unoptimized. Results The Pareto-optimal front generated showed a simultaneous maximization of the SE and EE of the SCMA-based HCN at high traffic levels and a convex front that allows network operators to select the SE-EE tradeoff at low traffic levels flexibly. The proposed PSO algorithm offers a higher SBS density, and a higher SBS transmit power at high traffic levels than at low traffic levels. The unoptimized SCMA-based HCN achieves an 80% lower SE and a 51% lower EE than the proposed PSO optimized SCMA-based HCN. The optimum SE and EE achieved by the SCMA-based HCN using the proposed PSO algorithm or the GA are comparable, but the proposed PSO uses a 51.85% lower SBS density and a 35.96% lower SBS transmit power to achieve the optimal SE and EE at moderate traffic levels. Conclusion In sleep-mode enabled SCMA-based HCNs, network engineers have to decide the balance of SBS density and SBS transmit power that helps achieve the desired SE and EE.Review Citation - WoS: 22Citation - Scopus: 39Cybersecurity Deep: Approaches, Attacks Dataset, and Comparative Study(Taylor & Francis inc, 2022) Barik, Kousik; Misra, Sanjay; Konar, Karabi; Fernandez-Sanz, Luis; Murat, Koyuncu; Koyuncu, MuratCyber attacks are increasing rapidly due to advanced digital technologies used by hackers. In addition, cybercriminals are conducting cyber attacks, making cyber security a rapidly growing field. Although machine learning techniques worked well in solving large-scale cybersecurity problems, an emerging concept of deep learning (DL) that caught on during this period caused information security specialists to improvise the result. The deep learning techniques analyzed in this study are convolution neural networks, recurrent neural networks, and deep neural networks in the context of cybersecurity.A framework is proposed, and a real-time laboratory setup is performed to capture network packets and examine this captured data using various DL techniques. A comparable interpretation is presented under the DL techniques with essential parameters, particularly accuracy, false alarm rate, precision, and detection rate. The DL techniques experimental output projects improvise the performance of various real-time cybersecurity applications on a real-time dataset. CNN model provides the highest accuracy of 98.64% with a precision of 98% with binary class. The RNN model offers the second-highest accuracy of 97.75%. CNN model provides the highest accuracy of 98.42 with multiclass class. The study shows that DL techniques can be effectively used in cybersecurity applications. Future research areas are being elaborated, including the potential research topics to improve several DL methodologies for cybersecurity applications.Article Citation - WoS: 44Citation - Scopus: 83Text Messaging-Based Medical Diagnosis Using Natural Language Processing and Fuzzy Logic(Hindawi Ltd, 2020) Omoregbe, Nicholas A. I.; Ndaman, Israel O.; Misra, Sanjay; Abayomi-Alli, Olusola O.; Damasevicius, RobertasThe use of natural language processing (NLP) methods and their application to developing conversational systems for health diagnosis increases patients' access to medical knowledge. In this study, a chatbot service was developed for the Covenant University Doctor (CUDoctor) telehealth system based on fuzzy logic rules and fuzzy inference. The service focuses on assessing the symptoms of tropical diseases in Nigeria. Telegram Bot Application Programming Interface (API) was used to create the interconnection between the chatbot and the system, while Twilio API was used for interconnectivity between the system and a short messaging service (SMS) subscriber. The service uses the knowledge base consisting of known facts on diseases and symptoms acquired from medical ontologies. A fuzzy support vector machine (SVM) is used to effectively predict the disease based on the symptoms inputted. The inputs of the users are recognized by NLP and are forwarded to the CUDoctor for decision support. Finally, a notification message displaying the end of the diagnosis process is sent to the user. The result is a medical diagnosis system which provides a personalized diagnosis utilizing self-input from users to effectively diagnose diseases. The usability of the developed system was evaluated using the system usability scale (SUS), yielding a mean SUS score of 80.4, which indicates the overall positive evaluation.

