Mısra, Sanjay
Loading...

Profile URL
Name Variants
M.,Sanjay
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Job Title
Profesör Doktor
Email Address
sanjay.misra@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Former Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
199
Articles
133
Views / Downloads
116/28
Supervised MSc Theses
3
Supervised PhD Theses
0
WoS Citation Count
2809
Scopus Citation Count
4101
Patents
0
Projects
0
WoS Citations per Publication
14.12
Scopus Citations per Publication
20.61
Open Access Source
53
Supervised Theses
3
| Journal | Count |
|---|---|
| Acta Polytechnica Hungarica | 12 |
| Tehnicki Vjesnik | 8 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 2011 International Conference on Computational Science and Its Applications, ICCSA 2011 -- 20 June 2011 through 23 June 2011 -- Santander -- 85480 | 5 |
| Journal of Physics: Conference Series -- 3rd International Conference on Computing and Applied Informatics 2018, ICCAI 2018 -- 18 September 2018 through 19 September 2018 -- Medan, Sumatera Utara -- 149865 | 4 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 12th International Conference on Computational Science and Its Applications, ICCSA 2012 -- 18 June 2012 through 21 June 2012 -- Salvador de Bahia -- 90945 | 4 |
Current Page: 1 / 22
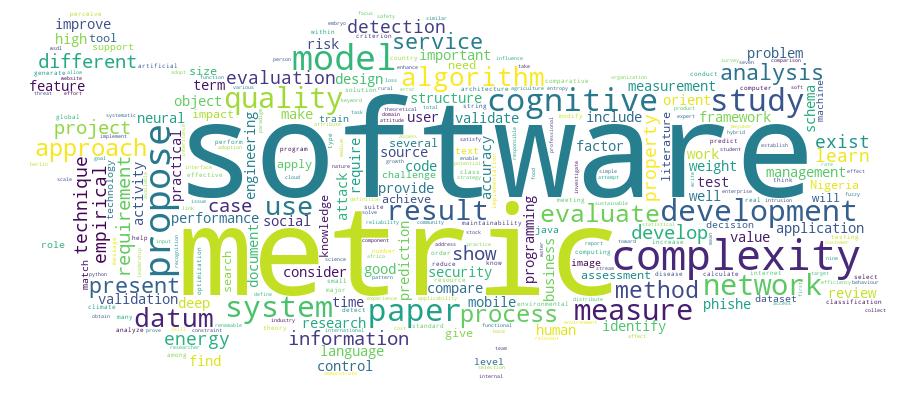
Competency Cloud