Mısra, Sanjay
Loading...

Profile URL
Name Variants
M.,Sanjay
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Misra, Sanjay
Mısra,S.
Mısra, Sanjay
Misra,S.
S.,Misra
Sanjay, Mısra
Sanjay, Misra
S., Misra
S.,Mısra
M., Sanjay
Misra, S.
Job Title
Profesör Doktor
Email Address
sanjay.misra@atilim.edu.tr
Main Affiliation
Computer Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
3
Research Products
 2
2ZERO HUNGER
5
Research Products
 3
3GOOD HEALTH AND WELL-BEING
2
Research Products
 4
4QUALITY EDUCATION
6
Research Products
 5
5GENDER EQUALITY
2
Research Products
 6
6CLEAN WATER AND SANITATION
1
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
8
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
11
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
11
Research Products
 10
10REDUCED INEQUALITIES
2
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
3
Research Products
 13
13CLIMATE ACTION
7
Research Products
 14
14LIFE BELOW WATER
10
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
4
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
9
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
199
Articles
133
Views / Downloads
719/275
Supervised MSc Theses
3
Supervised PhD Theses
0
WoS Citation Count
2781
Scopus Citation Count
4091
Patents
0
Projects
0
WoS Citations per Publication
13.97
Scopus Citations per Publication
20.56
Open Access Source
53
Supervised Theses
3
| Journal | Count |
|---|---|
| Acta Polytechnica Hungarica | 12 |
| Tehnicki Vjesnik | 8 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 2011 International Conference on Computational Science and Its Applications, ICCSA 2011 -- 20 June 2011 through 23 June 2011 -- Santander -- 85480 | 5 |
| Journal of Physics: Conference Series -- 3rd International Conference on Computing and Applied Informatics 2018, ICCAI 2018 -- 18 September 2018 through 19 September 2018 -- Medan, Sumatera Utara -- 149865 | 4 |
| Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) -- 12th International Conference on Computational Science and Its Applications, ICCSA 2012 -- 18 June 2012 through 21 June 2012 -- Salvador de Bahia -- 90945 | 4 |
Current Page: 1 / 22
Scopus Quartile Distribution
Competency Cloud
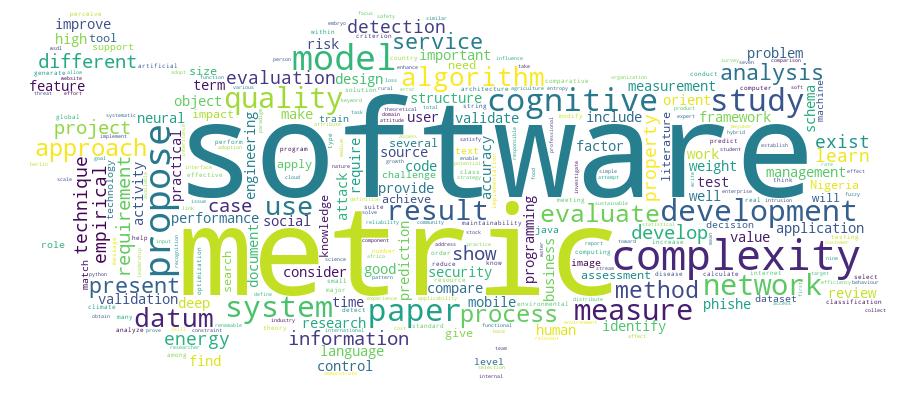
20 results
Scholarly Output Search Results
Now showing 1 - 10 of 20
Article Citation - WoS: 18Citation - Scopus: 35Distributed Centrality Analysis of Social Network Data Using Mapreduce(Mdpi, 2019) Behera, Ranjan Kumar; Rath, Santanu Kumar; Misra, Sanjay; Damasevicius, Robertas; Maskeliunas, RytisAnalyzing the structure of a social network helps in gaining insights into interactions and relationships among users while revealing the patterns of their online behavior. Network centrality is a metric of importance of a network node in a network, which allows revealing the structural patterns and morphology of networks. We propose a distributed computing approach for the calculation of network centrality value for each user using the MapReduce approach in the Hadoop platform, which allows faster and more efficient computation as compared to the conventional implementation. A distributed approach is scalable and helps in efficient computations of large-scale datasets, such as social network data. The proposed approach improves the calculation performance of degree centrality by 39.8%, closeness centrality by 40.7% and eigenvalue centrality by 41.1% using a Twitter dataset.Article Citation - WoS: 25Identifying Phishing Attacks in Communication Networks Using Url Consistency Features(inderscience Enterprises Ltd, 2020) Azeez, Nureni Ayofe; Salaudeen, Balikis Bolanle; Misra, Sanjay; Damasevicius, Robertas; Maskeliunas, RytisPhishing is a fraudulent attempt by cybercriminals, where the target audience is addressed by a text message, phone call or e-mail, requesting classified and sensitive information after presenting himself/herself as a legitimate agent. Successful phishing attack may result into financial loss and identity theft. Identifying forensic characteristics of phishing attack can help to detect the attack and its perpetuators and as well as to enable defence against it. To shield internet users from phishing assaults, numerous anti-phishing models have been proposed. Currently employed techniques to handle these challenges are not sufficient and capable enough. We aim at identifying phishing sites in order to guard internet users from being vulnerable to any form of phishing attacks by verifying the conceptual and literal consistency between the uniform resource locator (URL) and the web content. The implementation of the proposed PhishDetect method achieves an accuracy of 99.1%; indicating that it is effective in detecting various forms of phishing attacks.Article Citation - WoS: 23Citation - Scopus: 30Secure Ear Biometrics Using Circular Kernel Principal Component Analysis, Chebyshev Transform Hashing and Bose-Chaudhuri Error-Correcting Codes(Springer London Ltd, 2020) Olanrewaju, L.; Oyebiyi, Oyediran; Misra, Sanjay; Maskeliunas, Rytis; Damasevicius, RobertasEar biometrics has generated an increased interest in the domain of biometric identification systems due to its robustness and covert acquisition potential. The external structure of the human ear has a bilateral symmetry structure. Here, we analyse ear biometrics based on ear symmetry features. We apply iterative closest point and kernel principal component analysis with circular kernel for feature extraction while using a circular kernel function, combined with empirical mode decomposition into intrinsic mode functions perceptual hashing using and fast Chebyshev transform, and a secure authentication approach that exploits the discrete logarithm problem and Bose-Chaudhuri-Hocquenghem error-correcting codes to generate 128-bit crypto keys. We evaluate the proposed ear biometric cryptosecurity system using our data set of ear images acquired from 103 persons. Our results show that the ear biometric-based authentication achieved an equal error rate of 0.13 and true positive rate TPR of 0.85.Article Citation - WoS: 33Citation - Scopus: 51Optimizing Green Computing Awareness for Environmental Sustainability and Economic Security as a Stochastic Optimization Problem(Mdpi, 2017) Okewu, Emmanuel; Misra, Sanjay; Maskeliunas, Rytis; Damasevicius, Robertas; Fernandez-Sanz, LuisThe role of automation in sustainable development is not in doubt. Computerization in particular has permeated every facet of human endeavour, enhancing the provision of information for decision-making that reduces cost of operation, promotes productivity and socioeconomic prosperity and cohesion. Hence, a new field called information and communication technology for development (ICT4D) has emerged. Nonetheless, the need to ensure environmentally friendly computing has led to this research study with particular focus on green computing in Africa. This is against the backdrop that the continent is feared to suffer most from the vulnerability of climate change and the impact of environmental risk. Using Nigeria as a test case, this paper gauges the green computing awareness level of Africans via sample survey. It also attempts to institutionalize green computing maturity model with a view to optimizing the level of citizens awareness amid inherent uncertainties like low bandwidth, poor network and erratic power in an emerging African market. Consequently, we classified the problem as a stochastic optimization problem and applied metaheuristic search algorithm to determine the best sensitization strategy. Although there are alternative ways of promoting green computing education, the metaheuristic search we conducted indicated that an online real-time solution that not only drives but preserves timely conversations on electronic waste (e-waste) management and energy saving techniques among the citizenry is cutting edge. The authors therefore reviewed literature, gathered requirements, modelled the proposed solution using Universal Modelling Language (UML) and developed a prototype. The proposed solution is a web-based multi-tier e-Green computing system that educates computer users on innovative techniques of managing computers and accessories in an environmentally friendly way. We found out that such a real-time web-based interactive forum does not only stimulate the interest of the common man in environment-related issues, but also raises awareness about the impact his computer-related activities have on mother earth. This way, he willingly becomes part of the solution to environment degradation in his circle of influence.Article Citation - WoS: 116Citation - Scopus: 167Relationship Between Convenience, Perceived Value, and Repurchase Intention in Online Shopping in Vietnam(Mdpi, 2018) Quoc Trung Pham; Xuan Phuc Tran; Misra, Sanjay; Maskeliunas, Rytis; Damasevicius, Robertas; Tran, Xuan Phuc; Pham, Quoc TrungElectronic commerce (e-commerce) is an increasingly popular trend in modern economy concomitant with the development of the Internet. E-commerce has developed considerably, making Vietnam one of the fastest growing markets in the world. However, its growth rate has not matched its potential, leading to the question how online retailers could improve their practices and thus contribute to the sustainable development of emerging markets such as Vietnam. Therefore, with the goal of providing online retailers with many methods to improve their online shopping service, this study examined the direct and indirect influence of the dimensions of online shopping convenience on repurchase intention through customer-perceived value. A survey of 230 Vietnamese customers was conducted to test the theoretical model. A structural equation model was used for data analysis. The results determined that the five dimensions of online shopping convenience are: access, search, evaluation, transaction, and possession/post-purchase convenience. All dimensions have a direct impact on perceived value and repurchase intention. The results also show the important role of perceived value when a factor both directly influences repurchase intention and mediates the relationship between convenience and repurchase intention.Conference Object Embryo Spatial Model Reconstruction(Springer international Publishing Ag, 2020) Dirvanauskas, Darius; Maskeliunas, Rytis; Raudonis, Vidas; Misra, SanjayTime lapse microscopy offered new solutions to study embryo development process. It allows embryologist to monitor embryo growth in real time and evaluate them without interfering into their growth environment. Embryo evaluation during growth process is one of the key criteria in embryo selection for fertilization. Live embryo monitoring is time consuming and new tools are offered to automate part of process. Our proposed algorithm gives new possibilities for embryo monitoring. It uses embryo images which are taken from different embryo layers, extracts embryo cell features and returns metrical evaluation to compare different embryos. High number of extracted features shows embryo fragmentation. Other tool whichwe present is spatial embryo model. Features extracted from embryo layers are combined together to spatial model. It allows embryologist to examine embryo model and compare different layers in one space. The obtained spatial embryo model will be later used to develop new algorithms for embryo analysis tasks.Article Citation - WoS: 104Citation - Scopus: 163Cassava Disease Recognition From Low-Quality Images Using Enhanced Data Augmentation Model and Deep Learning(Wiley, 2021) Abayomi-Alli, Olusola Oluwakemi; Damasevicius, Robertas; Misra, Sanjay; Maskeliunas, RytisImprovement of deep learning algorithms in smart agriculture is important to support the early detection of plant diseases, thereby improving crop yields. Data acquisition for machine learning applications is an expensive task due to the requirements of expert knowledge and professional equipment. The usability of any application in a real-world setting is often limited by unskilled users and the limitations of devices used for acquiring images for classification. We aim to improve the accuracy of deep learning models on low-quality test images using data augmentation techniques for neural network training. We generate synthetic images with a modified colour value distribution to expand the trainable image colour space and to train the neural network to recognize important colour-based features, which are less sensitive to the deficiencies of low-quality images such as those affected by blurring or motion. This paper introduces a novel image colour histogram transformation technique for generating synthetic images for data augmentation in image classification tasks. The approach is based on the convolution of the Chebyshev orthogonal functions with the probability distribution functions of image colour histograms. To validate our proposed model, we used four methods (resolution down-sampling, Gaussian blurring, motion blur, and overexposure) for reducing image quality from the Cassava leaf disease dataset. The results based on the modified MobileNetV2 neural network showed a statistically significant improvement of cassava leaf disease recognition accuracy on lower-quality testing images when compared with the baseline network. The model can be easily deployed for recognizing and detecting cassava leaf diseases in lower quality images, which is a major factor in practical data acquisition.Article Citation - WoS: 25Citation - Scopus: 42Network Intrusion Detection With a Hashing Based Apriori Algorithm Using Hadoop Mapreduce(Mdpi, 2019) Azeez, Nureni Ayofe; Ayemobola, Tolulope Jide; Misra, Sanjay; Maskeliunas, Rytis; Damasevicius, RobertasUbiquitous nature of Internet services across the globe has undoubtedly expanded the strategies and operational mode being used by cybercriminals to perpetrate their unlawful activities through intrusion on various networks. Network intrusion has led to many global financial loses and privacy problems for Internet users across the globe. In order to safeguard the network and to prevent Internet users from being the regular victims of cyber-criminal activities, new solutions are needed. This research proposes solution for intrusion detection by using the improved hashing-based Apriori algorithm implemented on Hadoop MapReduce framework; capable of using association rules in mining algorithm for identifying and detecting network intrusions. We used the KDD dataset to evaluate the effectiveness and reliability of the solution. Our results obtained show that this approach provides a reliable and effective means of detecting network intrusion.Article Citation - WoS: 18Citation - Scopus: 24Fusion of Smartphone Sensor Data for Classification of Daily User Activities(Springer, 2021) Sengul, Gokhan; Ozcelik, Erol; Misra, Sanjay; Damasevicius, Robertas; Maskeliunas, RytisNew mobile applications need to estimate user activities by using sensor data provided by smart wearable devices and deliver context-aware solutions to users living in smart environments. We propose a novel hybrid data fusion method to estimate three types of daily user activities (being in a meeting, walking, and driving with a motorized vehicle) using the accelerometer and gyroscope data acquired from a smart watch using a mobile phone. The approach is based on the matrix time series method for feature fusion, and the modified Better-than-the-Best Fusion (BB-Fus) method with a stochastic gradient descent algorithm for construction of optimal decision trees for classification. For the estimation of user activities, we adopted a statistical pattern recognition approach and used the k-Nearest Neighbor (kNN) and Support Vector Machine (SVM) classifiers. We acquired and used our own dataset of 354 min of data from 20 subjects for this study. We report a classification performance of 98.32 % for SVM and 97.42 % for kNN.Article Citation - WoS: 23Citation - Scopus: 26Reconstruction of 3d Object Shape Using Hybrid Modular Neural Network Architecture Trained on 3d Models From Shapenetcore Dataset(Mdpi, 2019) Kulikajevas, Audrius; Maskeliunas, Rytis; Damasevicius, Robertas; Misra, SanjayDepth-based reconstruction of three-dimensional (3D) shape of objects is one of core problems in computer vision with a lot of commercial applications. However, the 3D scanning for point cloud-based video streaming is expensive and is generally unattainable to an average user due to required setup of multiple depth sensors. We propose a novel hybrid modular artificial neural network (ANN) architecture, which can reconstruct smooth polygonal meshes from a single depth frame, using a priori knowledge. The architecture of neural network consists of separate nodes for recognition of object type and reconstruction thus allowing for easy retraining and extension for new object types. We performed recognition of nine real-world objects using the neural network trained on the ShapeNetCore model dataset. The results evaluated quantitatively using the Intersection-over-Union (IoU), Completeness, Correctness and Quality metrics, and qualitative evaluation by visual inspection demonstrate the robustness of the proposed architecture with respect to different viewing angles and illumination conditions.

