Tora, Hakan
Loading...

Profile URL
Name Variants
Tora,H.
T., Hakan
Tora, Hakan
H., Tora
H.,Tora
T.,Hakan
Hakan, Tora
T., Hakan
Tora, Hakan
H., Tora
H.,Tora
T.,Hakan
Hakan, Tora
Job Title
Doktor Öğretim Üyesi
Email Address
hakan.tora@atilim.edu.tr
Main Affiliation
Airframe and Powerplant Maintenance
Status
Former Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
14
LIFE BELOW WATER

1
Research Products
2
ZERO HUNGER

0
Research Products
11
SUSTAINABLE CITIES AND COMMUNITIES

1
Research Products
1
NO POVERTY

0
Research Products
12
RESPONSIBLE CONSUMPTION AND PRODUCTION

0
Research Products
7
AFFORDABLE AND CLEAN ENERGY

2
Research Products
5
GENDER EQUALITY

0
Research Products
3
GOOD HEALTH AND WELL-BEING

1
Research Products
9
INDUSTRY, INNOVATION AND INFRASTRUCTURE

0
Research Products
13
CLIMATE ACTION

2
Research Products
6
CLEAN WATER AND SANITATION

0
Research Products
10
REDUCED INEQUALITIES

0
Research Products
4
QUALITY EDUCATION

0
Research Products
15
LIFE ON LAND

0
Research Products
16
PEACE, JUSTICE AND STRONG INSTITUTIONS

0
Research Products
17
PARTNERSHIPS FOR THE GOALS

1
Research Products
8
DECENT WORK AND ECONOMIC GROWTH

0
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
57
Articles
11
Views / Downloads
2/0
Supervised MSc Theses
14
Supervised PhD Theses
5
WoS Citation Count
57
Scopus Citation Count
88
WoS h-index
5
Scopus h-index
5
Patents
0
Projects
0
WoS Citations per Publication
1.00
Scopus Citations per Publication
1.54
Open Access Source
7
Supervised Theses
19
Google Analytics Visitor Traffic
| Journal | Count |
|---|---|
| 2014 22nd Signal Processing and Communications Applications Conference, SIU 2014 - Proceedings -- 2014 22nd Signal Processing and Communications Applications Conference, SIU 2014 -- 23 April 2014 through 25 April 2014 -- Trabzon -- 106053 | 3 |
| 22nd IEEE Signal Processing and Communications Applications Conference (SIU) -- APR 23-25, 2014 -- Karadeniz Teknik Univ, Trabzon, TURKEY | 3 |
| ICECS 2017 - 24th IEEE International Conference on Electronics, Circuits and Systems -- 24th IEEE International Conference on Electronics, Circuits and Systems, ICECS 2017 -- 5 December 2017 through 8 December 2017 -- Batumi -- 134675 | 2 |
| 24th IEEE International Conference on Electronics, Circuits and Systems (ICECS) -- DEC 05-08, 2017 -- Batumi, GEORGIA | 2 |
| 24th Signal Processing and Communication Application Conference (SIU) -- MAY 16-19, 2016 -- Zonguldak, TURKEY | 2 |
Current Page: 1 / 6
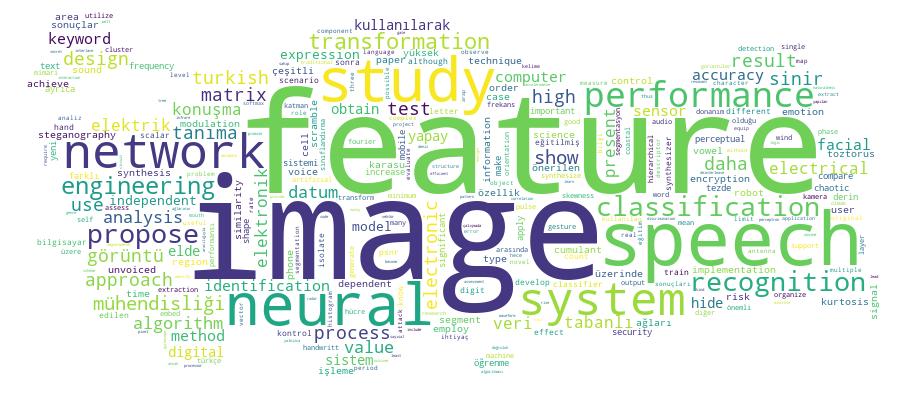
Competency Cloud