Gökçay, Erhan
Loading...
Profile URL
Name Variants
Gokcay, E
E.,Gökçay
Gökçay,E.
E., Gökçay
G.,Erhan
Gokcay E.
Goekcay, Erhan
Gokcay, Erhan
Erhan, Gokcay
Gökçay, Erhan
E., Gokcay
GOKCAY, E
Erhan, Gökçay
Gokcay,E.
Gökçay E.
G., Erhan
E.,Gokcay
E.,Gökçay
Gökçay,E.
E., Gökçay
G.,Erhan
Gokcay E.
Goekcay, Erhan
Gokcay, Erhan
Erhan, Gokcay
Gökçay, Erhan
E., Gokcay
GOKCAY, E
Erhan, Gökçay
Gokcay,E.
Gökçay E.
G., Erhan
E.,Gokcay
Job Title
Doktor Öğretim Üyesi
Email Address
erhan.gokcay@atilim.edu.tr
Main Affiliation
Software Engineering
Status
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals

Documents
16
Citations
395
h-index
7

Documents
15
Citations
293

Scholarly Output
21
Articles
6
Views / Downloads
2/0
Supervised MSc Theses
6
Supervised PhD Theses
2
WoS Citation Count
36
Scopus Citation Count
52
Patents
0
Projects
0
WoS Citations per Publication
1.71
Scopus Citations per Publication
2.48
Open Access Source
4
Supervised Theses
8
| Journal | Count |
|---|---|
| Multimedia Tools and Applications | 3 |
| 2017 IEEE 1st Ukraine Conference on Electrical and Computer Engineering, UKRCON 2017 - Proceedings -- 1st IEEE Ukraine Conference on Electrical and Computer Engineering, UKRCON 2017 -- 29 May 2017 through 2 June 2017 -- Kyiv -- 131763 | 1 |
| 24th IEEE International Conference on Electronics, Circuits and Systems (ICECS) -- DEC 05-08, 2017 -- Batumi, GEORGIA | 1 |
| 7th International Conference on Cloud Computing and Services Science (CLOSER) -- APR 24-26, 2017 -- Porto, PORTUGAL | 1 |
| 8th International Conference on Cloud Computing and Services Science (CLOSER) -- MAR 19-21, 2018 -- Funchal, PORTUGAL | 1 |
Current Page: 1 / 3
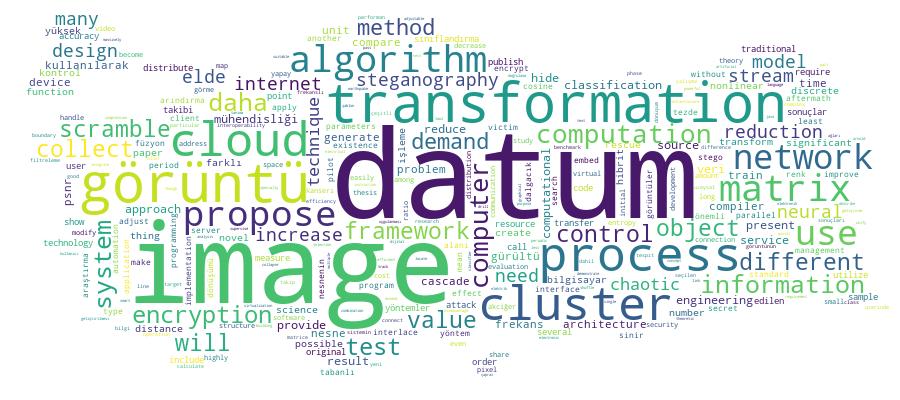
Competency Cloud